Systems Engineering and Electronics ›› 2026, Vol. 48 ›› Issue (1): 257-264.doi: 10.12305/j.issn.1001-506X.2026.01.23
• Systems Engineering • Previous Articles Next Articles
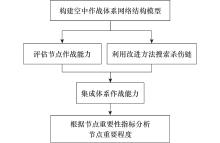
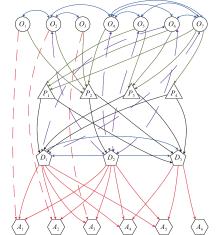
Important nodes recognition in the network of air combat system-of-system based on kill chain
Jintao YU1,*( ), Qiaolin HU1, Bing XIAO2, Po GAO1, Yanting TAO3
), Qiaolin HU1, Bing XIAO2, Po GAO1, Yanting TAO3
- 1. Department of Information Countermeasures,Air Force Early Warning Academy,Wuhan 430019,China
2. Department of Information Intelligence,Air Force Early Warning Academy,Wuhan 430019,China
3. Unit 94782 of the PLA,Hangzhou 311000,China
-
Received:2024-10-11Online:2026-01-25Published:2026-02-11 -
Contact:Jintao YU E-mail:haleine@ustc.edu
CLC Number:
Cite this article
Jintao YU, Qiaolin HU, Bing XIAO, Po GAO, Yanting TAO. Important nodes recognition in the network of air combat system-of-system based on kill chain[J]. Systems Engineering and Electronics, 2026, 48(1): 257-264.
share this article
Table 1
Types and meanings of the kill chain"
| 序号 | 类型 | 含义 |
| 1 | 察打一体杀伤链 | |
| 2 | 简化的杀伤链 | |
| 3 | 标准的杀伤链 | |
| 4 | 针对重要目标协同指控的杀伤链 | |
| 5 | 有简单反馈/信息引导的察打一体杀伤链 | |
| 6 | 有简单反馈的简化杀伤链 | |
| 7 | 有简单反馈的标准杀伤链 | |
| 8 | 有简单反馈的针对重要目标协同指控的杀伤链 | |
| 9 | 有标准反馈/信息引导的察打一体杀伤链 | |
| 10 | 有标准反馈的简化杀伤链 | |
| 11 | 有标准反馈的标准杀伤链 | |
| 12 | 有标准反馈的针对重要目标协同指控的杀伤链 |
Table 3
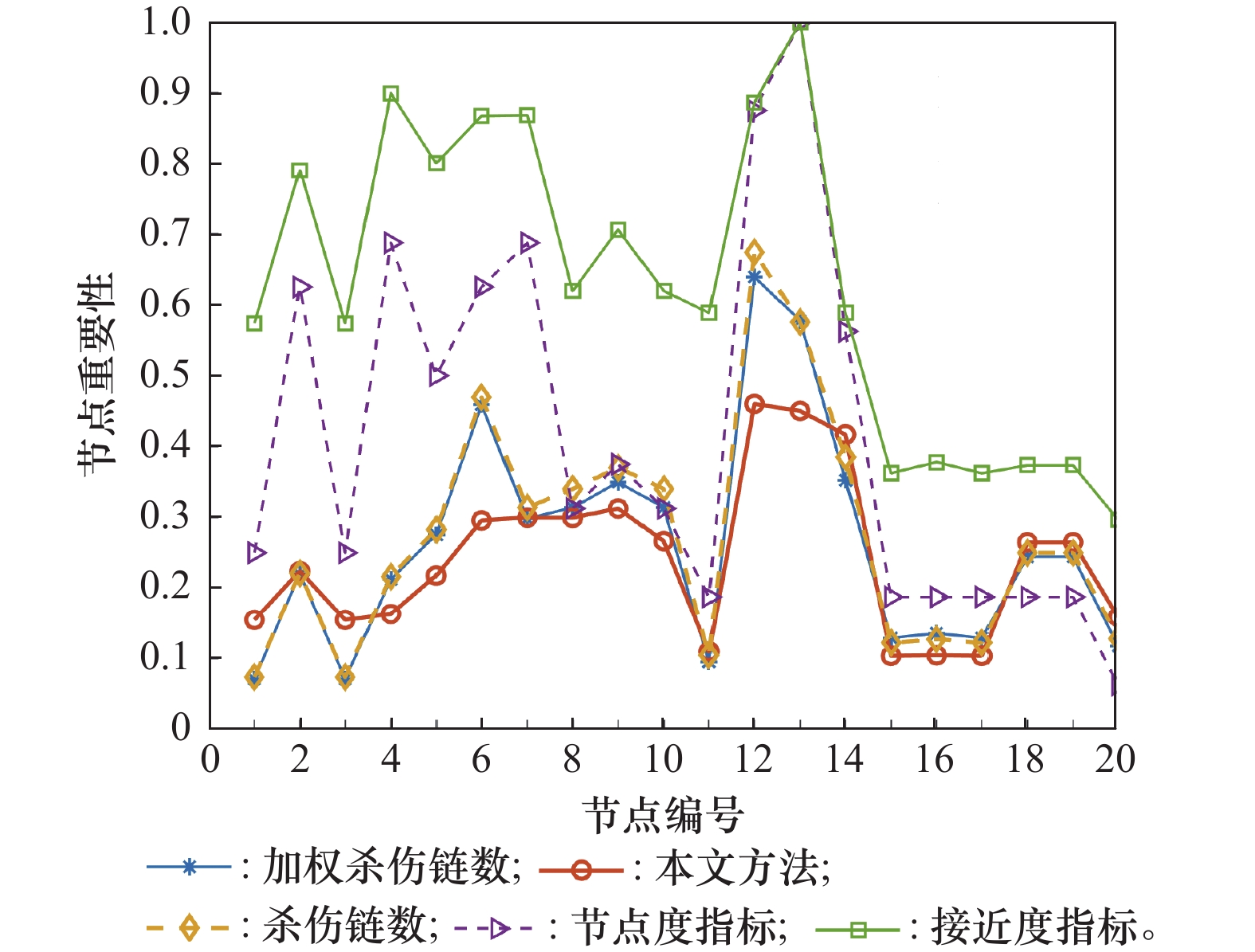
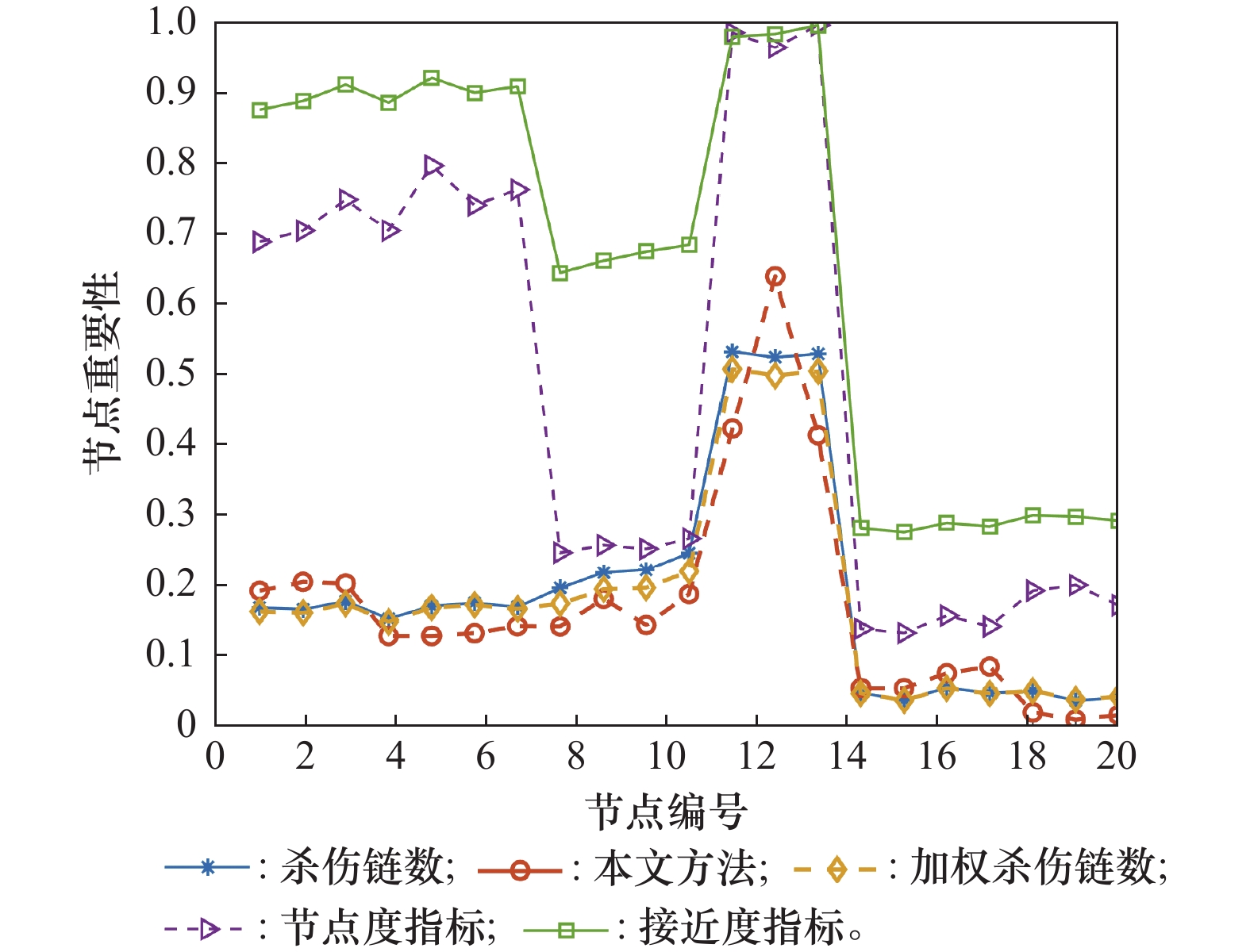
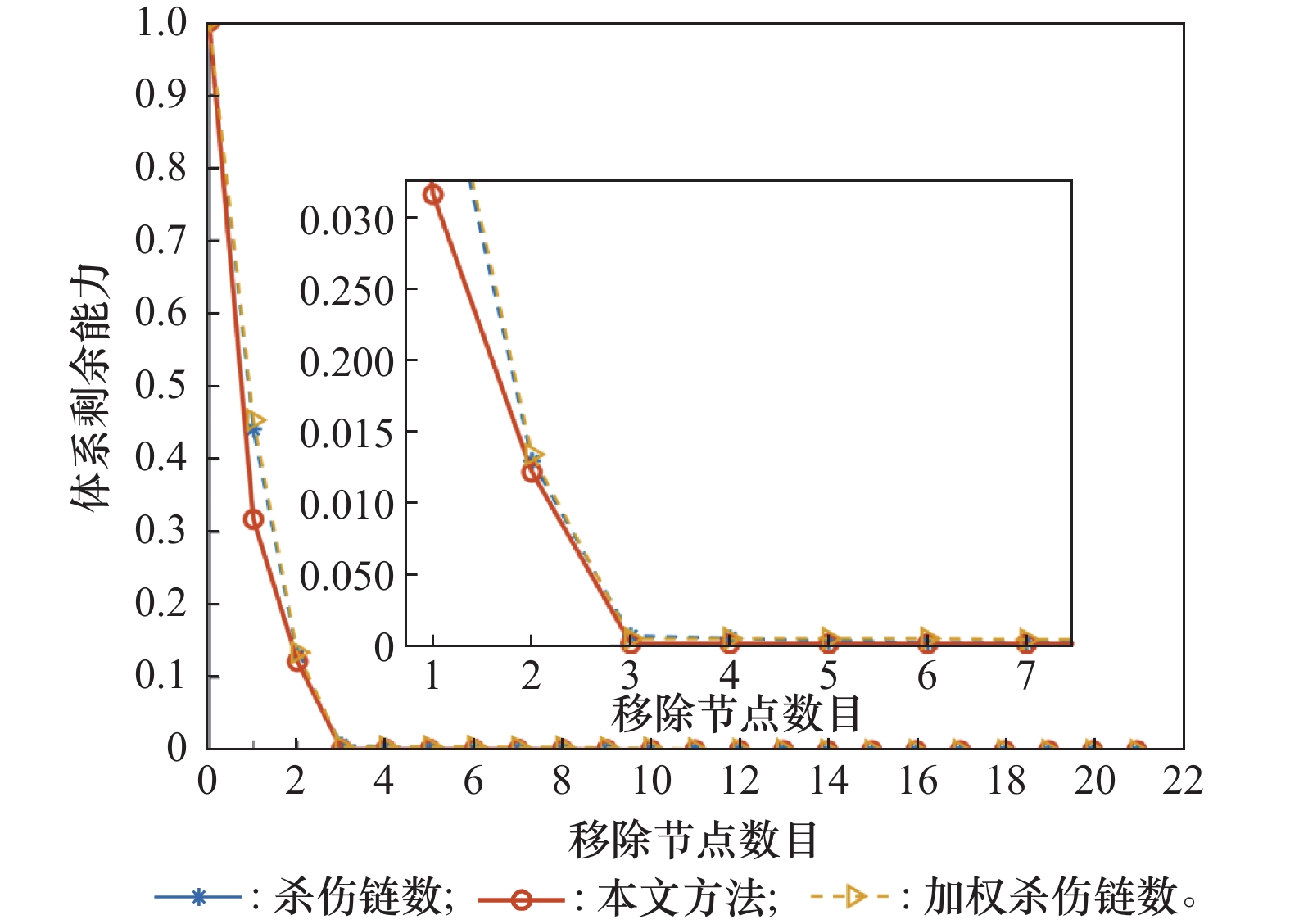
Ranks of network node importance of air combat system-of-system under a certain situation"
| 节点排序 | 杀伤链数 | 加权杀伤链数 | 本文方法 | 节点度指标 | 接近度指标 |
| 1 | D1 | D1 | D1 | D2 | D2 |
| 2 | D2 | D2 | D2 | D1 | O4 |
| 3 | O6 | O6 | D3 | O4 | D1 |
| 4 | D3 | D3 | P2 | O7 | O7 |
| 5 | P2 | P2 | O7 | O2 | O6 |
| 6 | P1 | P1 | P1 | O6 | O5 |
| 7 | P3 | P3 | O6 | D3 | O2 |
| 8 | O7 | O7 | P3 | O5 | P2 |
| 9 | O5 | O5 | A4 | P2 | P1 |
| 10 | A4 | A4 | A5 | P1 | P3 |
| 11 | A5 | A5 | O2 | P3 | D2 |
| 12 | O2 | O2 | O5 | O1 | P4 |
| 13 | O4 | O4 | O4 | O3 | O1 |
| 14 | A6 | A2 | A6 | P4 | O3 |
| 15 | A2 | A1 | O1 | A1 | A2 |
| 16 | A1 | A3 | O3 | A2 | A4 |
| 17 | A3 | A6 | P4 | A3 | A5 |
| 18 | P4 | P4 | A2 | A4 | A1 |
| 19 | O1 | O1 | A1 | A5 | A3 |
| 20 | O3 | O3 | A3 | A6 | A6 |
| 1 | SANKARAN J. The failures of Russian aerospace forces in the Russia–Ukraine war and the future of air power[J]. Journal of Strategic Studies, 2024, 47 (6): 860- 887. |
| 2 |
YITZHAK R. War in the air: Israel and Jordan in the dogfight[J]. Defence Studies, 2024, 24 (3): 365- 379.
doi: 10.1080/14702436.2024.2346503 |
| 3 | 俞锦涛, 肖兵, 熊家军. 基于拓扑势的网络毁伤最大算法[J]. 系统工程与电子技术, 2023, 45 (9): 2812- 2818. |
| YU J T, XIAO B, XIONG J J. Network damage maximization algorithm based on topology potential[J]. Systems Engineering and Electronics, 2023, 45 (9): 2812- 2818. | |
| 4 | 刘德胜. 基于复杂网络分析方法的作战体系评估研究综述[J]. 军事运筹与系统工程, 2020, 34 (3): 66- 73. |
| LIU D S. A survey of combat system assessment based on complex network analysis[J]. Military Operations Rsearch and Systems Engineering, 2020, 34 (3): 66- 73. | |
| 5 | BLOCH F, JACKSON M O, TEBALDI P. Centrality measures in networks[J]. Social Choice and Welfare, 2023, 61 (8): 413- 453. |
| 6 |
D’SOUZA R M, BERNARDO M D, LIU Y Y. Controlling complex networks with complex nodes[J]. Nature Reviews Physics, 2023, 5 (4): 250- 262.
doi: 10.1038/s42254-023-00566-3 |
| 7 | LIU Z F, YE J X, ZOU Z N. Closeness centrality on uncertain graphs[J]. ACM Transactions on the Web, 2023, 17 (4) 29. |
| 8 | UMUNNAKWE A, SAHU A, NARIMANI M R, et al. Cyber-physical component ranking for risk sensitivity analysis using betweenness centrality[J]. IET Cyber-Physical Systems: Theory & Applications, 2021, 6(3): 139−150. |
| 9 |
CHEN D B, LU L Y, SHANG M S, et al. Identifying influential nodes in complex networks[J]. Physica A: Statistical Mechanics and its Applications, 2012, 391 (4): 1777- 1787.
doi: 10.1016/j.physa.2011.09.017 |
| 10 |
LI G S, LI M, WANG J X, et al. United neighborhood closeness centrality and orthology for predicting essential proteins[J]. IEEE/ACM Trans. on Computational Biology and Bioinformatics, 2020, 17 (4): 1451- 1458.
doi: 10.1109/TCBB.2018.2889978 |
| 11 | DENG Y, WU J, TAN Y J. A fast connected component algorithm based on hub contraction[C]//Proc. of the IEEE International Conference on Systems, Man, and Cybernetics, 2016. |
| 12 | LU L Y, CHEN D B, REN X L, et al. Vital nodes identification in complex networks[J]. Physics Reports, 2016, 650 (9): 1- 63. |
| 13 | BOYD J R. A discourse on winning and losing[M]. Alabama: Air University Press, 2018. |
| 14 | MENG X Z, XIE C R, LI H, et al. Research on optimization of large-scale heterogeneous combat network based on graph embedding[J]. IEEE Access, 2025, 13: 5773−5784. |
| 15 | 杨倩, 方艳红, 锁斌. 基于OODA环的作战体系网络重要节点识别方法[J]. 探测与控制学报, 2023, 45 (6): 116- 122. |
| YANG Q, FANG Y H, SUO B. The important nodes identification of combat system network based on OODA ring[J]. Journal of Detection & Control, 2023, 45 (6): 116- 122. | |
| 16 |
俞锦涛, 肖兵, 熊家军. 基于效能环的预警情报体系能力评估[J]. 火力与指挥控制, 2022, 47 (2): 32- 36,42.
doi: 10.3969/j.issn.1002-0640.2022.02.006 |
|
YU J T, XIAO B, XIONG J J. Capability evaluation of early warning intelligence system-of-systems based on intelligence effectiveness loop[J]. Fire Control & Command Control, 2022, 47 (2): 32- 36,42.
doi: 10.3969/j.issn.1002-0640.2022.02.006 |
|
| 17 | 王耀祖, 尚柏林, 宋笔锋, 等. 基于杀伤链的作战体系网络关键节点识别方法[J]. 系统工程与电子技术, 2023, 45(3): 736−744. |
| WANG Y Z, SHANG B L, SONG B F, et al. Identification method of key node in operational system-of-systems network based on kill chain[J]. Systems Engineering and Electronics, 2023, 45(3): 736−744. | |
| 18 | BILTGEN P T. A methodology for capability-based technology evaluation for systems-of-systems[D]. Atlanta: Georgia Institute of Technology, 2007. |
| 19 | DUCHEINE P A, SCHMITT M N, OSINGA F P. Targeting: the challenges of modern warfare[M]. Netherlands: Asser Press, 2016. |
| 20 | BOYD J R. The essence of winning and losing[EB/OL]. [2024-09-23]. https://slightlyeastofnew.com/wp-content/uploads/2010/03/essence_of_winning_losing.pdf. |
| 21 | VALIENTE G. Algorithms on trees and graphs[M]. Berlin: Springer, 2021. |
| 22 |
BOURITSAS G, FRASCA F, ZAFEIRIOU S, et al. Improving graph neural network expressivity via subgraph isomorphism counting[J]. IEEE Trans. Pattern Analysis and Machine Intelligence, 2023, 45 (1): 657- 668.
doi: 10.1109/TPAMI.2022.3154319 |
| 23 | ULLMANN J R. An algorithm for subgraph isomorphism[J]. Journal of Association for Computer Magazine, 1976, 23 (1): 31- 42. |
| 24 |
CIBEJ U, MIHELIC J. Improvements to Ullmann’s algorithm for the subgraph isomorphism problem[J]. International Journal of Pattern Recognition and Artificial Intelligence, 2015, 29 (7): 1550025.
doi: 10.1142/S0218001415500251 |
| 25 | JUTTNER A, MADARASI P. VF2++—An improved subgraph isomorphism algorithm[J]. Discrete Applied Mathematics, 2018, 242 (6): 69- 81. |
| 26 | CARLETTI V, FOGGIA P, SAGGESE A, et al. Introducing VF3: a new algorithm for subgraph isomorphism[C]//Proc. of the Graph-based Representations in Pattern Recognition, 2017. |
| 27 | SOLNON C. AllDifferent-based filtering for subgraph isomorphism[J]. Artificial Intelligence, 2010, 174 (12): 850- 864. |
| 28 |
陆军, 张瑶, 乔永杰. 不确定性打击链的闭环时间表征和评估[J]. 中国科学·信息科学, 2017, 47 (2): 207- 220.
doi: 10.1360/N112016-00157 |
|
LU J, ZHANG Y, QIAO Y J. Representation and evaluation of the closed-loop time of the kill chain under uncertainties[J]. SCIENTIA SINICA Informationis, 2017, 47 (2): 207- 220.
doi: 10.1360/N112016-00157 |
|
| 29 |
LI J C, ZHAO D L, JIANG J, et al. Capability oriented equipment contribution analysis in temporal combat networks[J]. IEEE Trans. on Systems, Man, and Cybernetics: Systems, 2021, 51 (2): 696- 704.
doi: 10.1109/TCYB.2019.2914869 |
| 30 |
JACKIE C, DIANNE P, DUFFIELD C , et al. The Delphi method?[J]. Nursing Research, 1997, 46 (2): 116- 118.
doi: 10.1097/00006199-199703000-00010 |
| [1] | Xiangyu LIU, Gang WANG, Xiangke GUO, Qiang FU, Tengda LI. Kill chain design methodology for area air defense scenarios [J]. Systems Engineering and Electronics, 2025, 47(5): 1582-1599. |
| [2] | Song YANG, Tao WANG, Xiaobo LI, Hua HE, Jidong SUN. Modeling and evaluation of mission path generation in heterogeneous unmanned swarm kill-web [J]. Systems Engineering and Electronics, 2025, 47(10): 3278-3287. |
| [3] | Han ZHANG, Qiang WANG, Guilong MIN. Aviation safety risk early warning model based on mean field theory [J]. Systems Engineering and Electronics, 2025, 47(1): 210-216. |
| [4] | Tingyu ZHANG, Ying ZENG, Nan LI, Hongzhong HUANG. Spacecraft power-signal composite network optimization algorithm based on DRL [J]. Systems Engineering and Electronics, 2024, 46(9): 3060-3069. |
| [5] | Jintao YU, Bing XIAO, Jiajun XIONG. Network damage maximization algorithm based on topology potential [J]. Systems Engineering and Electronics, 2023, 45(9): 2812-2818. |
| [6] | Yanyan HUANG, Kaisheng WANG, Yu'ang SHI. Research on an evaluation model for data link operational support capability based on networking index [J]. Systems Engineering and Electronics, 2023, 45(8): 2361-2369. |
| [7] | Bingxue ZHANG, Xisheng LI, Jia YOU, Weiren SONG. End-edge collaborative network generation algorithm based on node composite characteristics [J]. Systems Engineering and Electronics, 2023, 45(8): 2588-2596. |
| [8] | Yaozu WANG, Bolin SHANG, Bifeng SONG, Pengfei LI, Erqin KE. Identification method of key node in operational system-of-systems network based on kill chain [J]. Systems Engineering and Electronics, 2023, 45(3): 736-744. |
| [9] | Xiangqian XU, Yajie DOU, Liwei QIAN, Jiang JIANG, Kewei YANG, Yuejin TAN. Research on agile development method-of-combat system-of-systems capability requirements [J]. Systems Engineering and Electronics, 2023, 45(10): 3139-3148. |
| [10] | Tong HUANG, Qinhe GAO, Zhihao LIU, Dong WANG, Dong MA, Lei GAO. Topological properties of launch platform anti-damage network based on complex network theory [J]. Systems Engineering and Electronics, 2023, 45(10): 3157-3164. |
| [11] | Shunqi HUAN, Zhemei FAN, Jianbo WANG. System-of-systems effectiveness evaluation method based on functional dependency network [J]. Systems Engineering and Electronics, 2022, 44(7): 2191-2200. |
| [12] | Tongliang LU, Wenhao CHEN, Bingfeng GE, Qiling DENG. Multi-layer network modeling for combat system-of-systems under information support [J]. Systems Engineering and Electronics, 2022, 44(2): 520-528. |
| [13] | Cong WANG, Huiliang SHEN, Yongxiang XIA, Guanghan BAI, Yining FANG. Analysis of critical nodes in equipment support system [J]. Systems Engineering and Electronics, 2022, 44(10): 3134-3142. |
| [14] | Yantao WANG, Zheng YANG. Propagation and control improvement of flight operation risk network [J]. Systems Engineering and Electronics, 2021, 43(9): 2544-2552. |
| [15] | Guangxun ZENG, Guanghong GONG, Ni LI. Combat system-of-systems simulation scenario generation approach based on semantic matching [J]. Systems Engineering and Electronics, 2021, 43(8): 2154-2162. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||