Systems Engineering and Electronics ›› 2023, Vol. 45 ›› Issue (3): 876-885.doi: 10.12305/j.issn.1001-506X.2023.03.30
• Communications and Networks • Previous Articles Next Articles
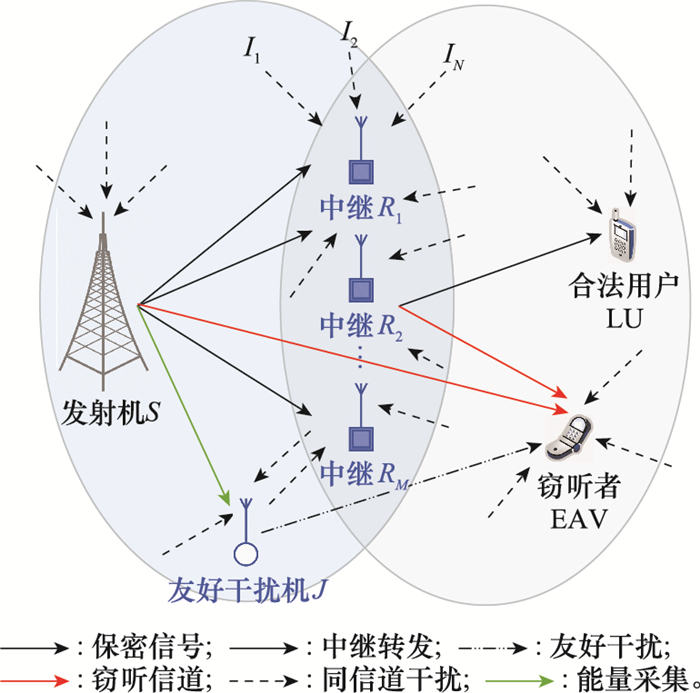
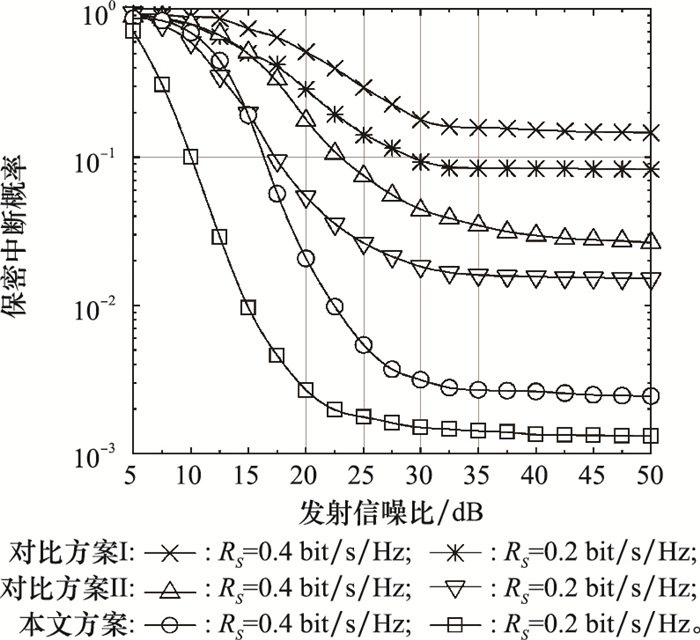
Security transmission scheme for multi-relay system with a friendly jammer-assisted based on energy harvesting
Guangda ZHANG1,*, Qinghua REN1,2, Zhikai FAN1
- 1. Information and Navigation College, Air Force Engineering University, Xi'an 710077, China
2. Key Laboratory of Aerospace Information Applications, China Electronics Technology Group CorporationShijiazhuang 050081, China
-
Received:2021-09-24Online:2023-02-25Published:2023-03-09 -
Contact:Guangda ZHANG
CLC Number:
Cite this article
Guangda ZHANG, Qinghua REN, Zhikai FAN. Security transmission scheme for multi-relay system with a friendly jammer-assisted based on energy harvesting[J]. Systems Engineering and Electronics, 2023, 45(3): 876-885.
share this article
| 1 | WANG D , BAI B , ZHAO W B , et al. A survey of optimization approaches for wireless physical layer security[J]. IEEE Communications Surveys & Tutorials, 2019, 21 (2): 1878- 1911. |
| 2 | VAISHNAVI K N, KHORVI S D, KISHORE R, et al. A survey on jamming techniques in physical layer security and anti-jamming strategies for 6G[C]//Proc. of the IEEE 28th International Conference on Telecommunications, 2021: 174-179. |
| 3 | JAMEEL F , WYNE S , KADDOUM G , et al. A comprehensive survey on cooperative relaying and jamming strategies for physical layer security[J]. IEEE Communications Surveys & Tutorials, 2019, 21 (3): 2734- 2771. |
| 4 |
WANG H M , XIA X G . Enhancing wireless secrecy via cooperation: signal design and optimization[J]. IEEE Communications Magazine, 2015, 53 (12): 47- 53.
doi: 10.1109/MCOM.2015.7355565 |
| 5 |
CAO Z H , JI X D , WANG J , et al. Security-reliability trade-off analysis of AN-aided relay selection for full-duplex relay networks[J]. IEEE Trans. on Vehicular Technology, 2021, 70 (3): 2362- 2377.
doi: 10.1109/TVT.2021.3057830 |
| 6 |
KAMBOJ A K , JINDAL P , VERMA P . Intelligent physical layer secure relay selection for wireless cooperative networks with multiple eavesdroppers[J]. Wireless Personal Communications, 2021, 120, 2449- 2472.
doi: 10.1007/s11277-021-08458-4 |
| 7 |
FENG Y H , YAN S H , LIU C X , et al. Two-stage relay selection for enhancing physical layer security in non-orthogonal multiple access[J]. IEEE Trans. on Information Forensics and Security, 2019, 14 (6): 1670- 1683.
doi: 10.1109/TIFS.2018.2883273 |
| 8 |
DATTA R , GURJAR D S , REDDY T K M , et al. Secrecy performance of amplify-and-forward relay networks with relay selection under Nakagamim fading[J]. Wireless Personal Communications, 2020, 112 (4): 2233- 2251.
doi: 10.1007/s11277-020-07147-y |
| 9 |
LIU C X , YANG N , MALANEY R , et al. Artificial-noise-aided transmission in multi-antenna relay wiretap channels with spatially random eavesdroppers[J]. IEEE Trans. on Wireless Communications, 2016, 15 (11): 7444- 7456.
doi: 10.1109/TWC.2016.2602337 |
| 10 |
LEE K , BANG J , CHOI H H . Secrecy outage minimization for wireless-powered relay networks with destination-assisted cooperative jamming[J]. IEEE Internet of Things Journal, 2021, 8 (3): 1467- 1476.
doi: 10.1109/JIOT.2020.3013573 |
| 11 | 邹羿, 黄开枝, 康小磊. 基于中继间干扰消除的轮流转发系统安全传输方案[J]. 通信学报, 2017, 38 (9): 185- 192. |
| ZOU Y , HUANG K Z , KANG X L . Successive relaying secure transmission scheme based on inter-relay interference cancellation[J]. Journal on Communications, 2017, 38 (9): 185- 192. | |
| 12 |
CHEN X M , CHEN J , ZHANG H Z , et al. On secrecy performance of multiantenna-jammer-aided secure communications with imperfect CSI[J]. IEEE Trans. on Vehicular Technology, 2016, 65 (10): 8014- 8024.
doi: 10.1109/TVT.2015.2510502 |
| 13 |
CAO K R , WANG B H , DING H Y , et al. On the security enhancement of uplink NOMA systems with jammer selection[J]. IEEE Trans. on Communications, 2020, 68 (9): 5747- 5763.
doi: 10.1109/TCOMM.2020.3003665 |
| 14 |
SI J B , CHENG Z H , LI Z , et al. Cooperative jamming for secure transmission with both active and passive eavesdroppers[J]. IEEE Trans. on Communications, 2020, 68 (9): 5764- 5777.
doi: 10.1109/TCOMM.2020.3003946 |
| 15 | 李敏, 林敏. 同信道干扰条件下的多天线放大转发中继中断概率分析[J]. 电子与信息学报, 2015, 37 (1): 163- 168. |
| LI M , LIN M . Outage probability analysis of dual-hop MIMO amplify-and-forward relaying with multiple co-channel interferences[J]. Journal of Electronics & Information Technology, 2015, 37 (1): 163- 168. | |
| 16 |
XIANG Z W , YANG W W , CAI Y M , et al. NOMA-assisted secure short-packet communications in IoT[J]. IEEE Wireless Communications, 2020, 27 (4): 8- 15.
doi: 10.1109/MWC.01.1900529 |
| 17 |
SSETTUMBA T , ABD EL-MALEK A H , ELSABROUTY M , et al. Physical layer security enhancement for internet of things in the presence of co-channel interference and multiple eavesdroppers[J]. IEEE Internet of Things Journal, 2019, 6 (4): 6441- 6452.
doi: 10.1109/JIOT.2019.2907574 |
| 18 |
LI B , ZHOU J J , ZOU Y L , et al. Security and reliability trade-off analysis of joint user and jammer selection in the face of co-channel interference[J]. IET Communications, 2019, 13 (16): 2601- 2608.
doi: 10.1049/iet-com.2019.0438 |
| 19 |
LI B , ZHOU J J , ZOU Y L , et al. Closed-form secrecy outage analysis of cellular downlink systems in the presence of co-channel interference[J]. IEEE Trans. on Wireless Communications, 2018, 17 (7): 4721- 4734.
doi: 10.1109/TWC.2018.2830383 |
| 20 |
MOUALEU J M , HAMOUDA W , TAKAWIRA F . Intercept probability analysis of wireless networks in the presence of eavesdropping attack with co-channel interference[J]. IEEE Access, 2018, 6, 41490- 41503.
doi: 10.1109/ACCESS.2018.2854222 |
| 21 |
FAN L S , LEI X F , YANG N , et al. Secure multiple amplify-and-forward relaying with cochannel interference[J]. IEEE Journal of Selected Topics in Signal Processing, 2016, 10 (8): 1494- 1505.
doi: 10.1109/JSTSP.2016.2607692 |
| 22 |
TUAN V P , KONG H Y . Exploiting cooperative relays to enhance the performance of energy-harvesting systems over Nakagamim fading channels[J]. Telecommunication Systems, 2018, 69 (4): 477- 487.
doi: 10.1007/s11235-018-0448-y |
| 23 | 裴二荣, 易鑫, 邓炳光, 等. D2D辅助的窄带物联网中能耗和传输成功率的最优折中[J]. 电子与信息学报, 2020, 42 (12): 2915- 2922. |
| PEI E R , YI X , DENG B G , et al. The optimal tradeoff between energy consumption and transmission success probability in D2D assisted narrow band-internet of things[J]. Journal of Electronics & Information Technology, 2020, 42 (12): 2915- 2922. | |
| 24 |
CAO K R , WANG B H , DING H Y , et al. Adaptive cooperative jamming for secure communication in energy harvesting relay networks[J]. IEEE Wireless Communications Letters, 2019, 8 (5): 1316- 1319.
doi: 10.1109/LWC.2019.2914108 |
| 25 | 孔槐聪, 林敏, 刘笑宇, 等. 基于中继选择的星地协作传输系统性能分析[J]. 系统工程与电子技术, 2020, 42 (1): 198- 205. |
| KONG H C , LIN M , LIU X Y , et al. Performance analysis of hybrid satellite-terrestrial cooperative transmission system based on relay selection[J]. Systems Engineering and Electronics, 2020, 42 (1): 198- 205. | |
| 26 | GRADSHTEǏN I S , ZWILLINGER D . Table of integrals, series, and products[M]. 8th ed New York: Academic Press, 2014. |
| 27 |
SONG K , NIE M Y , JIANG J , et al. On the secrecy for relay-aided SWIPT internet of things system with cooperative eavesdroppers[J]. IEEE Access, 2021, 9, 28204- 28212.
doi: 10.1109/ACCESS.2021.3058504 |
| 28 |
GUO H Y , YANG Z , ZHANG L H , et al. Power-constrained secrecy rate maximization for joint relay and jammer selection assisted wireless networks[J]. IEEE Trans. on Communications, 2017, 65 (5): 2180- 2193.
doi: 10.1109/TCOMM.2017.2651066 |
| [1] | Siqi TANG, Zhisong PAN, Guyu HU, Yang WU, Yunbo LI. Application of deep reinforcement learning in space information network——status quo and prospects [J]. Systems Engineering and Electronics, 2023, 45(3): 886-901. |
| [2] | Dong XIA, Kaixuan ZHANG, Youbao DING, Baopeng LI. Co-channel interference resistance based on agile wave form of phase encode and CFAR technology [J]. Systems Engineering and Electronics, 2022, 44(4): 1210-1219. |
| [3] | Yin LU, Gaoyu WANG, Chuying YANG, Lingqing YANG, Kun ZHAO, Hongbo ZHU. NOMA relay selection and cooperative transmission based on single source optimal path [J]. Systems Engineering and Electronics, 2022, 44(1): 292-298. |
| [4] | Danyu DIAO, Buhong WANG, Kunrui CAO, Runze DONG, Tianhao CHENG. Secrecy performance analysis of UAV-based communications against full-duplex eavesdropping [J]. Systems Engineering and Electronics, 2022, 44(1): 313-319. |
| [5] | Chonglin HE, Ziwen SUN. Multi-level Stackelberg game model against full-duplex attacking node in IWSN physical layer [J]. Systems Engineering and Electronics, 2021, 43(10): 2931-2939. |
| [6] | Jianbang GAO, Zhaohui YUAN, Bin QIU. Physical-layer security wireless transmission synthesis scheme for proximal desired receiver user and eavesdropper [J]. Systems Engineering and Electronics, 2020, 42(5): 1160-1165. |
| [7] | Hong ZOU, Bin WAN, Dapeng WU. Edge cooperative relay mechanism with cooperative willingness aware [J]. Systems Engineering and Electronics, 2020, 42(5): 1173-1181. |
| [8] | Huaicong KONG, Min LIN, Xiaoyu LIU, Xuewen WU, Jinyuan WANG. Performance analysis of hybrid satellite-terrestrial cooperative transmission system based on relay selection [J]. Systems Engineering and Electronics, 2020, 42(1): 198-205. |
| [9] | LI Min, WANG Pingshan, WANG Kaili. Selection cooperation based on packet aggregation in multi-source multi-destination networks [J]. Systems Engineering and Electronics, 2019, 41(5): 1149-1155. |
| [10] | ZHU Jiang, WANG Zhihao. TRAN-SWIPT energy efficiency secure transmission scheme based on Lyapulov optimization [J]. Systems Engineering and Electronics, 2019, 41(12): 2879-2884. |
| [11] | YUAN Tian, TAO Jianfeng, LI Xingcheng. Main lobe track deception jamming method based on association rule [J]. Systems Engineering and Electronics, 2018, 40(2): 273-279. |
| [12] | LEI Weijia, YANG Xiaoyan, LIN Xiuzhen. Secure transmission scheme based on SWIPT relay with antenna grouping [J]. Systems Engineering and Electronics, 2017, 39(8): 1849-1856. |
| [13] | WANG Heng, WEI Xinyu, LI Min. Relay selection methods for multi-source and multi-destination cooperative networks [J]. Systems Engineering and Electronics, 2017, 39(6): 1358-1365. |
| [14] | LU Zhizhong, ZHOU Ying, HUANG Yu. Research on correlation in spatial domain to eliminate the co-channel interference of the X-band marine radar [J]. Systems Engineering and Electronics, 2017, 39(4): 758-767. |
| [15] | FU Xiao-mei, YAO Xiao-ming, ZONG Qun. Relay selection and power optimization in cooperative coalitions [J]. Systems Engineering and Electronics, 2016, 38(5): 1176-. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||