Systems Engineering and Electronics ›› 2022, Vol. 44 ›› Issue (10): 3155-3163.doi: 10.12305/j.issn.1001-506X.2022.10.19
• Systems Engineering • Previous Articles Next Articles
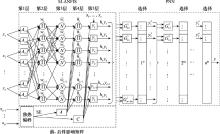
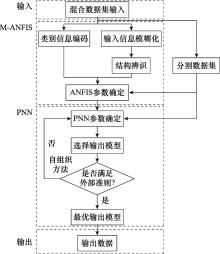
Target threat assessment model based on M-ANFIS-PNN
Bowen YU, Lin YU, Ming LYU*, Jie ZHANG
- School of Automation, Nanjing University of Science and Technology, Nanjing 210094, China
-
Received:2021-11-10Online:2022-09-20Published:2022-10-24 -
Contact:Ming LYU
CLC Number:
Cite this article
Bowen YU, Lin YU, Ming LYU, Jie ZHANG. Target threat assessment model based on M-ANFIS-PNN[J]. Systems Engineering and Electronics, 2022, 44(10): 3155-3163.
share this article
Table 2
Value range and attribute value of the target characteristic attribute"
| 编号 | 特征属性 | 取值范围及属性值 | 特征类别 |
| 1 | D/m | [500, 6 000] | 定量数值 |
| 2 | V/(km/h) | [0, 150] | 定量数值 |
| 3 | CA/(°) | [-180, 180] | 定量数值 |
| 4 | H/m | [0, 2 000] | 定量数值 |
| 5 | FR/km | [0, 50] | 定量数值 |
| 6 | AC/(m/s2) | [ | 定量数值 |
| 7 | C | 武装直升机C1, 主战坦克C2, 自行火炮C3, 步兵战车C4, 装甲作战指挥车C5, 导弹发射车C6 | 定性分类 |
| 8 | A | 一级攻击状态A1, 二级攻击状态A2, 三级攻击状态A3 | 定性分类 |
| 9 | DS | 未被毁伤D1, 轻度毁伤D2, 中度毁伤D3, 重度毁伤D4, 报废D5 | 定性分类 |
| 10 | CC | 特强CC1, 强CC2, 较强CC3, 一般CC4, 较弱CC5, 弱CC6, 特弱CC7 | 定性分类 |
Table 3
Incoming target feature information"
| 编号 | D/m | V/(km/h) | CA/(°) | H/m | FR/km | AC/(m/s2) | C | A | DS | CC | R |
| 1 | 2 800 | 60 | 10 | 0 | 3 | 3.5 | C5 | A3 | DS1 | CC1 | 0.994 1 |
| 2 | 1 500 | 10 | 15 | 5 | 3.2 | 2.5 | C2 | A1 | DS1 | CC6 | 0.943 1 |
| 3 | 1 000 | 0 | 5 | 10 | 3.2 | 2 | C2 | A1 | DS1 | CC6 | 0.969 9 |
| 4 | 3 500 | 60 | 120 | 5 | 3.5 | 2.5 | C2 | A3 | DS2 | CC6 | 0.321 4 |
| 5 | 2 500 | 30 | 120 | 8 | 4 | 2 | C2 | A3 | DS2 | CC6 | 0.392 7 |
| 6 | 2 500 | 60 | 5 | 11 | 2 | 2 | C2 | A2 | DS1 | CC6 | 0.727 6 |
| 7 | 1 000 | 5 | 5 | 100 | 3 | 1 | C1 | A1 | DS1 | CC3 | 0.979 4 |
| 8 | 3 000 | 60 | 50 | 400 | 5 | 1 | C1 | A2 | DS1 | CC3 | 0.854 7 |
| 9 | 5 200 | 150 | 5 | 800 | 3 | 1.5 | C1 | A3 | DS2 | CC4 | 0.546 2 |
| 10 | 6 000 | 130 | 150 | 300 | 3 | 0.8 | C1 | A3 | DS3 | CC4 | 0.154 3 |
| 11 | 4 200 | 100 | 30 | 300 | 6 | 1.5 | C1 | A3 | DS2 | CC4 | 0.347 7 |
| 12 | 1 300 | 0 | 5 | 20 | 10 | 0.5 | C3 | A1 | DS1 | CC6 | 0.914 2 |
| 13 | 1 500 | 5 | 5 | 2 | 8 | 0.4 | C3 | A1 | DS2 | CC6 | 0.905 8 |
| 14 | 3 800 | 60 | 20 | 6 | 8 | 0.4 | C3 | A2 | DS2 | CC6 | 0.432 9 |
| 15 | 2 000 | 0 | 30 | 21 | 10 | 0.4 | C3 | A2 | DS5 | CC6 | 0.119 1 |
| 16 | 3 500 | 60 | 160 | 5 | 10 | 0.5 | C3 | A3 | DS3 | CC6 | 0.136 7 |
| 17 | 1 800 | 18 | 40 | 5 | 3 | 3 | C4 | A2 | DS2 | CC3 | 0.721 9 |
| 18 | 1 500 | 0 | 15 | 5 | 3 | 3 | C4 | A2 | DS5 | CC3 | 0.125 6 |
Table 4
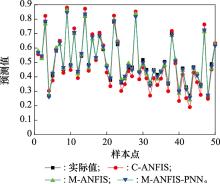
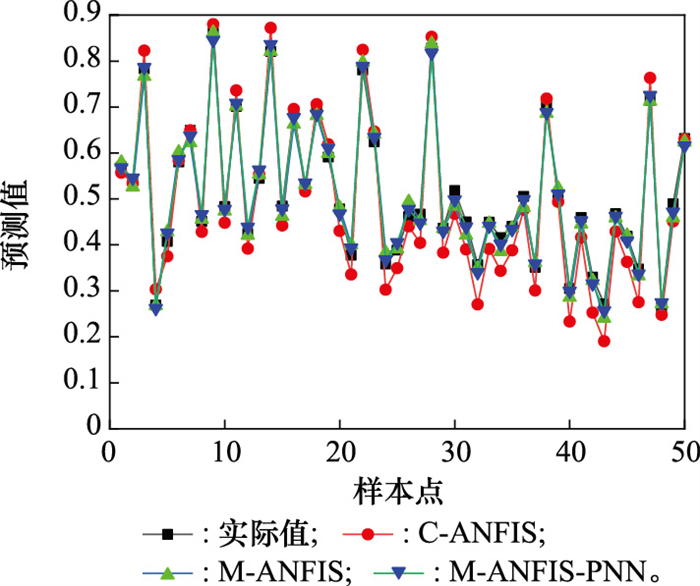
C-ANFIS(C), M-ANFIS(M), M-ANFIS-PNN (M+PNN) algorithm performance comparison"
| 实验数据 | 模型 | 性能评价指标 | ||||
| R | MSE | RMSE | E-Mean | E-StD | ||
| 训练数据 | C | 0.913 | 0.697 | 0.835 | 0.099 | 0.836 |
| M | 0.921 | 0.511 | 0.714 | 0.073 | 0.715 | |
| M+PNN | 0.955 | 0.371 | 0.609 | 0.053 | 0.611 | |
| 数据阶段 | C | 0.862 | 0.874 | 0.935 | 0.124 | 0.936 |
| M | 0.871 | 0.741 | 0.861 | 0.105 | 0.862 | |
| M+PNN | 0.918 | 0.537 | 0.733 | 0.076 | 0.734 | |
| 全部数据 | C | 0.887 | 0.785 | 0.885 | 0.112 | 0.886 |
| M | 0.896 | 0.626 | 0.787 | 0.089 | 0.788 | |
| M+PNN | 0.936 | 0.454 | 0.673 | 0.064 | 0.674 | |
| 1 | 靳崇, 孙娟, 王永佳, 等. 基于直觉模糊TOPSIS和变权VIKOR的防空目标威胁综合评估[J]. 系统工程与电子技术, 2022, 44 (1): 172- 180. |
| JIN C , SUN J , WANG Y J , et al. Threat comprehensive assessment for air defense targets based on intuitionistic fuzzy TOPSIS and variable weight VIKOR[J]. Systems Engineering and Electronics, 2022, 44 (1): 172- 180. | |
| 2 | QU C W, HE Y. A method of threat assessment using multiple attribute decision making[C]//Proc. of the 6th International Confe-rence on Signal Processing, 2002, 2: 1091-1095. |
| 3 | 卢盈齐, 范成礼, 付强, 等. 基于改进IFRS相似度和信息熵的反导作战目标威胁评估[J]. 系统工程与电子技术, 2022, 44 (4): 1230- 1238. |
| LU Y Q , FAN C L , FU Q , et al. Missile defense target threat assessment based on improved similarity measure and information entropy of intuitionistic fuzzy rough sets[J]. Systems Engineering and Electronics, 2022, 44 (4): 1230- 1238. | |
| 4 | 赵烨南, 杜伟伟, 陈铁健, 等. 基于集对分析的坦克多目标威胁评估方法[J]. 火力与指挥控制, 2020, 45 (6): 108- 112. |
| ZHAO Y N , DU W W , CHEN T J , et al. Multi-target threat assessment method of tank based on set pair analysis[J]. Fire Control & Command Control, 2020, 45 (6): 108- 112. | |
| 5 |
柴慧敏, 张勇, 李欣粤, 等. 基于深度学习的空中目标威胁评估方法[J]. 系统仿真学报, 2022, 34 (7): 1459- 1467.
doi: 10.16182/j.issn1004731x.joss.21-0080 |
|
CHAI H M , ZHANG Y , LI X Y , et al. Aerial target threat assessment method based on deep learning[J]. Journal of System Simulation, 2022, 34 (7): 1459- 1467.
doi: 10.16182/j.issn1004731x.joss.21-0080 |
|
| 6 |
孔尚萍, 张海瑞, 廖选平, 等. 基于AHP与熵权法的空中目标威胁评估方法[J]. 战术导弹技术, 2018, (1): 79- 84.
doi: 10.16358/j.issn.1009-1300.2018.01.14 |
|
KONG S P , ZHANG H R , LIAO X P , et al. Aerial targets threat assessment based on AHP and entropy weight method[J]. Tactical Missile Technology, 2018, (1): 79- 84.
doi: 10.16358/j.issn.1009-1300.2018.01.14 |
|
| 7 |
LUO R N , HUANG S C , ZHAO Y , et al. Threat assessment method of low altitude slow small (LSS) targets based on information entropy and AHP[J]. Entropy, 2021, 23 (10): 1292.
doi: 10.3390/e23101292 |
| 8 |
任耀军, 袁修久, 黄林, 等. 毕达哥拉斯三角犹豫模糊Muirhead平均算子的目标威胁评估应用[J]. 电光与控制, 2021, 28 (4): 16- 20.16-20, 63
doi: 10.3969/j.issn.1671-637X.2021.04.004 |
|
REN Y J , YUAN X J , HUANG L , et al. Pythagorean hesitant triangular fuzzy muirhead mean operator and its application in target threat assessment[J]. Electronics Optics & Control, 2021, 28 (4): 16- 20.16-20, 63
doi: 10.3969/j.issn.1671-637X.2021.04.004 |
|
| 9 | 赵若静, 杨风暴, 吉琳娜. 基于可能性理论扩展灰关联的目标威胁评估[J]. 指挥信息系统与技术, 2021, 12 (3): 23- 29. |
| ZHAO R J , YANG F B , JI L N . Target threat assessment based on extended grey correlation with possibility theory[J]. Command Information System and Technology, 2021, 12 (3): 23- 29. | |
| 10 |
JANG J S R . ANFIS: adaptive-network-based fuzzy inference system[J]. IEEE Trans.on Systems, Man, and Cybernetics, 1993, 23 (3): 665- 685.
doi: 10.1109/21.256541 |
| 11 | LIU M , DONG M Y , WU C . A new ANFIS for parameter prediction with numeric and categorical inputs[J]. IEEE Trans.on Automation Science and Engineering, 2010, 7 (3): 645- 653. |
| 12 |
ARMAGHANI D J , HARANDIZADEH H , MOMENI E . Load carrying capacity assessment of thin-walled foundations: an ANFIS-PNN model optimized by genetic algorithm[J]. Engineering with Computers, 2021,
doi: 10.1007/s00366-21-01380-0 |
| 13 | FREY B J , DUECK D . Clustering by passing messages between data points[J]. Science, 2007, 315 (5814): 972- 976. |
| 14 | MADANDOUST R , BUNGEY J H , GHAVIDEL R . Prediction of the concrete compressive strength by means of core testing using GMDH-type neural network and ANFIS models[J]. Computational Materials Science, 2012, 51 (1): 261- 272. |
| 15 | HARANDIZADEH H , ARMAGHANI D J , ASTERIS P G , et al. TBM performance prediction developing a hybrid ANFIS-PNN predictive model optimized by imperialism competitive algorithm[J]. Neural Computing and Applications, 2021, 33 (23): 16149- 16179. |
| 16 | JIA X D , DI Y , FENG J S , et al. Adaptive virtual metrology for semiconductor chemical mechanical planarization process using GMDH-type polynomial neural networks[J]. Journal of Process Control, 2018, 62, 44- 54. |
| 17 | HUANG W , OH S K , PEDRYCZ W . Fuzzy reinforced polynomial neural networks constructed with the aid of PNN architecture and fuzzy hybrid predictor based on nonlinear function[J]. Neurocomputing, 2021, 458, 454- 467. |
| 18 | ARMAGHANI D J , HARANDIZADEH H , MOMENI E , et al. An optimized system of GMDH-ANFIS predictive model by ICA for estimating pile bearing capacity[J]. Artificial Intelligence Review, 2022, 55 (3): 2313- 2350. |
| 19 | HARANDIZADEH H , TOUFIGH M M , TOUFIGH V . Application of improved ANFIS approaches to estimate bearing capacity of piles[J]. Soft Computing, 2019, 23 (19): 9537- 9549. |
| 20 | GAN G J , NG M K P . Subspace clustering using affinity pro-pagation[J]. Pattern Recognition, 2015, 48 (4): 1455- 1464. |
| 21 | HU Q , ZHANG Q , SI X S , et al. Intelligent fault diagnosis approach based on composite multi-scale dimensionless indicators and affinity propagation clustering[J]. IEEE Sensors Journal, 2020, 20 (19): 11439- 11453. |
| 22 | AHMAD A , KHAN S S . Survey of state-of-the-art mixed data clustering algorithms[J]. IEEE Access, 2019, 7, 31883- 31902. |
| 23 | ZHANG K , GU X S . An affinity propagation clustering algorithm for mixed numeric and categorical datasets[J]. Mathematical Problems in Engineering, 2014, 486075. |
| 24 | BEKTAS A, SCHUMANN R. How to optimize Gower distance weights for the k-medoids clustering algorithm to obtain mobility profiles of the Swiss population[C]//Proc. of the 6th Swiss Conference on Data Science, 2019: 51-56. |
| 25 | FOSS A H , MARKATOU M , RAY B . Distance metrics and clustering methods for mixed type data[J]. International Statistical Review, 2019, 87 (1): 80- 109. |
| 26 | AKAY O , YUKSEL G . Hierarchical clustering of mixed variable panel data based on new distance[J]. Communications in Statistics-Simulation and Computation, 2019, 50 (6): 1695- 1710. |
| 27 | CHENG Y M , JIA H . Categorical and numerical attribute data clustering based on a unified similarity metric without knowing cluster number[J]. Pattern Recognition, 2013, 46 (8): 2228- 2238. |
| 28 | QUE X , JIANG S Y , YANG J Y , et al. A similarity measurement with entropy-based weighting for clustering mixed numerical and categorical datasets[J]. Algorithms, 2021, 14 (6): 184. |
| 29 | HARANDIZADEH H , ARMAGHANI D J . Prediction of air-overpressure induced by blasting using an ANFIS-PNN model optimized by GA[J]. Applied Soft Computing, 2021, 99, 106904. |
| 30 | HARANDIZADEH H , JAHED A D , KHARI M . A new development of ANFIS-GMDH optimized by PSO to predict pile bearing capacity based on experimental datasets[J]. Engineering with Computers, 2021, 37 (1): 685- 700. |
| [1] | Xinyu XU, Lunjun WAN, Ping CHEN, Jiangbin DAI, Zhizhou GAO. Modeling of alert patrol airspace planning in defensive counterair interception operation [J]. Systems Engineering and Electronics, 2022, 44(5): 1589-1599. |
| [2] | Yingqi LU, Chengli FAN, Qiang FU, Xiaowen ZHU, Wei LI. Missile defense target threat assessment based on improved similarity measure and information entropy of IFRS [J]. Systems Engineering and Electronics, 2022, 44(4): 1230-1238. |
| [3] | Chong JIN, Juan SUN, Yongjia WANG, Pushen CAI, Xin RONG. Threat comprehensive assessment for air defense targets based on intuitionistic fuzzy TOPSIS and variable weight VIKOR [J]. Systems Engineering and Electronics, 2022, 44(1): 172-180. |
| [4] | Yunke SUN, Zhigeng FANG, Ding CHEN. Multi-time threat assessment based on dynamic grey principal component analysis [J]. Systems Engineering and Electronics, 2021, 43(3): 740-746. |
| [5] | Guanglei MENG, Mingzhe ZHOU, Haiyin PIAO, Huimin ZHANG. Threat assessment method of dual-aircraft formation based on cooperative tactical recognition [J]. Systems Engineering and Electronics, 2020, 42(10): 2285-2293. |
| [6] | SUN Haiwen, XIE Xiaofang, SUN Tao, ZHANG Longjie. Threat assessment method of warships formation air defense based on DBN under the condition of small sample data missing [J]. Systems Engineering and Electronics, 2019, 41(6): 1300-1308. |
| [7] | SUN Qingpeng, LI Zhanwu, CHANG Yizhe. Multi-types airplane threat assessment based on combat power field [J]. Systems Engineering and Electronics, 2018, 40(9): 1993-1999. |
| [8] | XU Ximeng, YANG Rennong, FU Ying, ZHAO Yu. Target threat assessment in air combat based on ELM_AdaBoost strong predictor [J]. Systems Engineering and Electronics, 2018, 40(8): 1760-1768. |
| [9] | ZHANG Ying, WANG Hongwei, CHEN You. Combined emitter threat assessment based on ICWM-RCM [J]. Systems Engineering and Electronics, 2018, 40(3): 557-562. |
| [10] | OUYANG Zhihong, XUE Lei, DING Feng. Jamming target assignment method of regional electronic air defense against electrooptical precision guided weapon#br# [J]. Systems Engineering and Electronics, 2018, 40(12): 2621-2628. |
| [11] | SUN Haiwen, XIE Xiaofang, SUN Tao, ZHANG Longjie. Threat assessment method of warships formation air defense based on DDBN-cloud model [J]. Systems Engineering and Electronics, 2018, 40(11): 2466-. |
| [12] | ZHANG Haowei, XIE Junwei, GE Jiaang, ZHANG Zhaojian, ZONG Binfeng. Intuitionistic fuzzy set threat assessment based on improved TOPSIS and multiple times fusion#br# [J]. Systems Engineering and Electronics, 2018, 40(10): 2263-2269. |
| [13] | TANG Xin, YANG Jianjun, FENG Song, REN Baoxiang. AR(p) dynamic catastrophe ranking method of target threat assessment under the loss of data [J]. Systems Engineering and Electronics, 2017, 39(5): 1058-1064. |
| [14] | ZHANG Cai-kun, ZHU Zhan-xia, FENG Qi, ZHANG Kun. Visualization threat assessment for air combat based on interval-radar chart [J]. Systems Engineering and Electronics, 2016, 38(5): 1052-. |
| [15] | CHEN Jieyu, YAO Peiyang, WANG Bo, SHUI Dongdong. Dynamic threat assessment based on structure entropy and IGSO-BP algorithm [J]. Systems Engineering and Electronics, 2015, 37(5): 1076-1083. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||