Systems Engineering and Electronics ›› 2022, Vol. 44 ›› Issue (8): 2652-2660.doi: 10.12305/j.issn.1001-506X.2022.08.31
• Communications and Networks • Previous Articles Next Articles
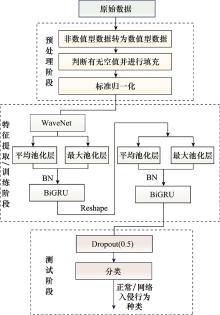
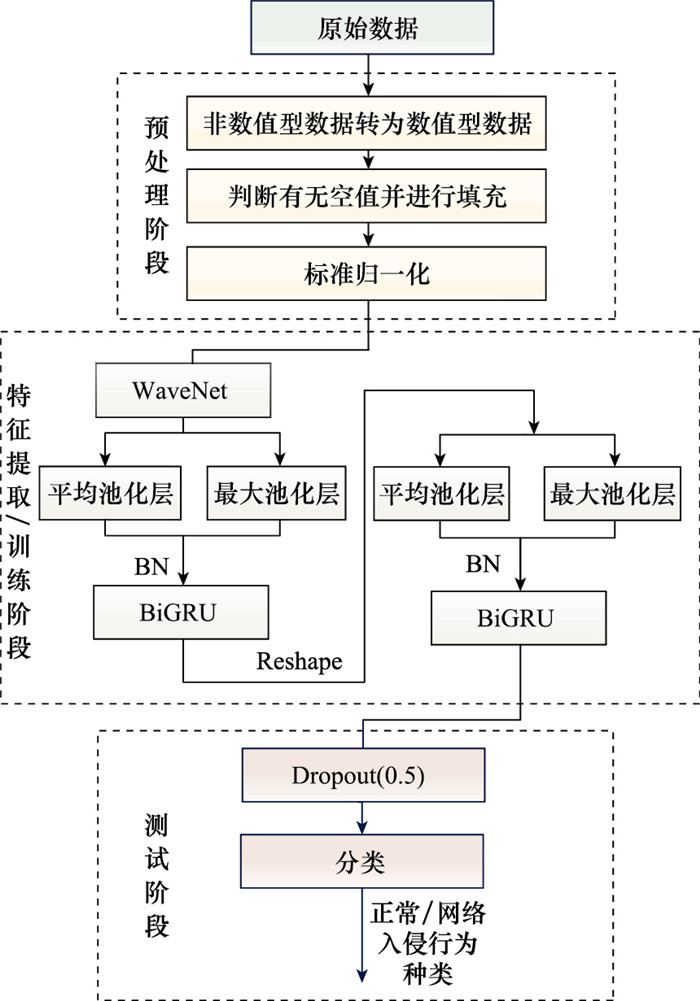
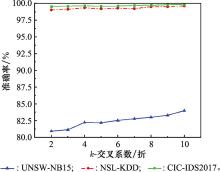
Network intrusion detection method based on WaveNet and BiGRU
Zexuan MA1, Jin LI1, Yanli LU1,*, Chen CHEN2
- 1. School of Air and Missile Defense, Air Force Engineering University, Xi'an 710051, China
2. Xi'an Satellite Control Center, Xi'an 710043, China
-
Received:2021-06-03Online:2022-08-01Published:2022-08-24 -
Contact:Yanli LU
CLC Number:
Cite this article
Zexuan MA, Jin LI, Yanli LU, Chen CHEN. Network intrusion detection method based on WaveNet and BiGRU[J]. Systems Engineering and Electronics, 2022, 44(8): 2652-2660.
share this article
| 1 |
MOHAMED A F , LEANDROS M , SOTIRIS M , et al. Deep learning for cyber security intrusion detection: approaches, datasets, and comparative study[J]. Journal of Information Security and Applications, 2020,
doi: 10.1016/j.jisa.2019.102419 |
| 2 | HAO S Y, LONG J, YANG Y C. Detecting web attacks using Bi-LSTM model based on deep learning[C]//Proc. of the International Conference on Security and Privacy in New Computing Environments, 2019: 551-563. |
| 3 | KIM J Y, KIM J, THU H L T, et al. Long short term memory recurrent neural network classifier for intrusion detection[C]//Proc. of the International Conference on Platform Technology and Service, 2016. |
| 4 |
SUN P F , LIU P J , LI Q , et al. Extracting features using CNN-LSTM hybrid network for intrusion detection system[J]. Security and Communication Networks, 2020,
doi: 10.1155/2020/8890306 |
| 5 | 谢康. 基于神经网络的入侵检测相关技术研究[D]. 济南: 山东大学, 2016. |
| XIE K. Research on intrusion detection technology based on neural network[D]. Ji'nan: Shandong University, 2016. | |
| 6 |
DORADO R F , DURÁN S J . Short-term load forecasting using encoder-decoder WaveNet: application to the French grid[J]. Energies, 2021,
doi: 10.3390/en14092524 |
| 7 | 谢潇雨. 基于卷积神经网络的入侵检测模型研究[D]. 南京: 南京邮电大学, 2019. |
| XIE X Y. Research on intrusion detection model based on convolutional neural network[D]. Nanjing: Nanjing University of Posts and Telecommunications, 2019. | |
| 8 | WANG H , CAO Z J , HONG B . A network intrusion detection system based on convolutional neural network[J]. Journal of Intelligent & Fuzzy Systems, 2020, 38 (6): 7623- 7637. |
| 9 |
ARIAV I , COHEN I . An end-to-end multimodal voice activity detection using WaveNet encoder and residual networks[J]. IEEE Journal of Selected Topics in Signal Processing, 2019, 13 (2): 265- 274.
doi: 10.1109/JSTSP.2019.2901195 |
| 10 |
CHEN Y S , FENG N X , HONG B B , et al. Express WaveNet: a lower parameter optical neural network with random shift wavelet pattern[J]. Optics Communications, 2021, 485, 126709.
doi: 10.1016/j.optcom.2020.126709 |
| 11 | YUAN X Y, LI C H, LI X L. Deep defense: identifying DDOS attack via deep learning[C]//Proc. of the IEEE International Conference on Smart Computing, 2017. |
| 12 | RAI A. Optimizing a new intrusion detection system using ensemble methods and deep neural network[C]//Proc. of the 4th International Conference on Trends in Electronics and Informatics, 2020. |
| 13 | WANKHEDE S, KSHIRSAGAR D. DOS attack detection using machine learning and neural network[C]//Proc. of the 4th International Conference on Computing Communication Control and Automation, 2018. |
| 14 |
GONG Y L , LU N , ZHANG J J . Application of deep learning fusion algorithm in natural language processing in emotional semantic analysis[J]. Concurrency and Computation: Practice and Experience, 2019, 31 (10): e4779.
doi: 10.1002/cpe.4779 |
| 15 | 周航, 凌捷. 改进的基于BiLSTM的网络入侵检测方法[J]. 计算机工程与设计, 2020, 41 (7): 1809- 1814. |
| ZHOU H , LING J . Improved network intrusion detection method based on BiLSTM[J]. Computer Engineering and Design, 2020, 41 (7): 1809- 1814. | |
| 16 | RAN Z Y , ZHENG D S , LAI Y L , et al. Applying stack bidirectional LSTM model to intrusion detection[J]. CMC-Computers Materials & Continua, 2020, 65 (1): 309- 320. |
| 17 |
YAN X , SHI Z M , WANG G C , et al. Detection of possible hydrological precursor anomalies using long short-term memory: a case study of the 1996 Lijiang earthquake[J]. Journal of Hydrology, 2021,
doi: 10.1016/j.jhydrol.2021.126369 |
| 18 | AZAM R, MUHAMMAD J S, SHAHID M A. Machine and deep learning based comparative analysis using hybrid approaches for intrusion detection system[C]//Proc. of the 3rd International Conference on Advancements in Computational Sciences, 2020. |
| 19 |
SINGH N B , SINGH M M , SARKAR A , et al. A novel wide & deep transfer learning stacked GRU framework for network intrusion detection[J]. Journal of Information Security and Applications, 2021,
doi: 10.1016/j.jisa.2021.102899 |
| 20 |
YAN B H , HAN G D . LA-GRU: building combined intrusion detection model based on imbalanced learning and gated recurrent unit neural network[J]. Security and Communication Networks, 2018,
doi: 10.1155/2018/6026878 |
| 21 | KAMAL A , ABULAISH M . CAT-BiGRU: convolution and attention with bi-directional gated recurrent unit for self-deprecating sarcasm detection[J]. Cognitive Computation, 2021, 14, 1- 19. |
| 22 | SONG Y , LI Z L , CHENG C . ARP attack intrusion detection method of industrial control system based on CNN-BILSTM[J]. Computer Application Research, 2020, 37 (S2): 242- 244. |
| 23 | DÜDÜKÇÜ H V, TAŞKIRAN M, KAHRAMAN N. LSTM and WaveNet implementation for predictive maintenance of turbofan engines[C]//Proc. of the IEEE 20th International Symposium on Computational Intelligence and Informatics, 2020. |
| 24 | ISHAQUE M, HUDEC L. Feature extraction using deep learning for intrusion detection system[C]//Proc. of the 2nd International Conference on Computer Applications & Information Security, 2019. |
| 25 | ACHARYA T, KHATRI I, ANNAMALAI A, et al. Efficacy of machine learning-based classifiers for binary and multi-class network intrusion detection[C]//Proc. of the IEEE International Conference on Automatic Control & Intelligent Systems, 2021. |
| 26 |
SARIKA C K , NISHTHA K . Analysis of KDD-cup′99, NSL-KDD and UNSW-NB15 datasets using deep learning in IoT[J]. Procedia Computer Science, 2020, 167, 1561- 1573.
doi: 10.1016/j.procs.2020.03.367 |
| 27 | KOCHER G , GUISHAN K A . Analysis of machine learning algorithms with feature selection for intrusion detection using UNSW-NB15 dataset[J]. International Journal of Network Security & Its Applications, 2021, 13 (1): 21- 31. |
| 28 |
HOOGE D L , WAUTERS T , VOLCKAERT B , et al. Inter-dataset generalization strength of supervised machine learning methods for intrusion detection[J]. Journal of Information Security and Applications, 2020,
doi: 10.1016/j.jisa.2020.102564 |
| 29 | KAJAL R S D M , AJAY G . Decision tree based algorithm for intrusion detection[J]. International Journal of Advanced Networking and Applications, 2016, 7 (4): 2828- 2834. |
| 30 | 夏景明, 李冲, 谈玲, 等. 改进的随机森林分类器网络入侵检测方法[J]. 计算机工程与设计, 2019, 40 (8): 2146- 2150. |
| XIA J M , LI C , TAN L , et al. Improved intrusion detection method of random forest classifier network[J]. Computer Engineering and Design, 2019, 40 (8): 2146- 2150. | |
| 31 | 李俊, 夏松竹, 兰海燕, 等. 基于GRU-RNN的网络入侵检测方法[EB/OL]. 哈尔滨工程大学学报, 2021. DOI: 10.4218/etrij.2019-0476. |
| LI J, XIA S Z, LAN H Y, et al. Network intrusion detection method based on GRU-RNN[EB/OL]. Journal of Harbin Engineering University, 2021. DOI: 10.4218/etrij.2019-0476. | |
| 32 | JAY S M, MANOLLAS. Efficient deep CNN-BILSTM model for network intrusion detection[C]//Proc. of the 3rd International Conference on Artificial Intelligence and Pattern Recognition, 2020. |
| [1] | Haoliang LI, Siwei CHEN, Xuesong WANG. Study on characterization of sea corner reflectors in polarimetric rotation domain [J]. Systems Engineering and Electronics, 2022, 44(7): 2065-2073. |
| [2] | Feng ZHU, Qianqian JIANG, Chuan LIN, Xiao YANG. Typical wideband EMI identification based on support vector machine [J]. Systems Engineering and Electronics, 2021, 43(9): 2400-2406. |
| [3] | Zhigang JIN, Tong WU. Intrusion detection based on feature selection and tree Parzen estimation [J]. Systems Engineering and Electronics, 2021, 43(7): 1954-1960. |
| [4] | Li WANG, Ziqi LIU. Fault diagnosis of analog circuit for WPA-IGA-BP neural network [J]. Systems Engineering and Electronics, 2021, 43(4): 1133-1143. |
| [5] | Hao CHEN, Jun'an YANG, Hui LIU. Communication transmitter individual identification based on deep residual adaptation network [J]. Systems Engineering and Electronics, 2021, 43(3): 603-609. |
| [6] | Guoling ZHANG, Chongming WU, Rui LI, Jie LAI, Qian XIANG. HRRP target recognition method based on one-dimensional stacked pooling fusion convolutional autoencoder [J]. Systems Engineering and Electronics, 2021, 43(12): 3533-3541. |
| [7] | Ruochen ZHAO, Jingdong WANG, Siyu LIN, Dongze GU. Small building detection algorithm based on convolutional neural network [J]. Systems Engineering and Electronics, 2021, 43(11): 3098-3106. |
| [8] | Tianqi ZHANG, Congcong FAN, Shengqi YU, Jiangen ZHAO. Blind recognition of orthogonal and non-orthogonal space-time block codes based on JADE and feature extraction [J]. Systems Engineering and Electronics, 2020, 42(4): 933-939. |
| [9] | Jiadong YI, Jie YANG. Radar signal recognition based on IFOA-SA-BP neural network [J]. Systems Engineering and Electronics, 2020, 42(12): 2735-2741. |
| [10] | Bo LI, Lin ZHANG, Wenfeng WANG, Guannan WANG. Fault feature extraction method based on Park-HHT [J]. Systems Engineering and Electronics, 2020, 42(12): 2944-2952. |
| [11] | Zhangwen FANG, Jinyi ZHANG, Ke LI, Yuxi JIANG. Semi-supervised feature extraction of communication emitter under small sample condition [J]. Systems Engineering and Electronics, 2020, 42(10): 2381-2389. |
| [12] | LIU Ying, TIAN Runlan, WANG Xiaofeng. Radar signal recognition method based on deep convolutional neural network and bispectrum feature [J]. Systems Engineering and Electronics, 2019, 41(9): 1998-2005. |
| [13] | LIU Lifang, YANG Haixia, QI Xiaogang. Time-frequency domain feature extraction algorithm based on linear discriminant analysis [J]. Systems Engineering and Electronics, 2019, 41(10): 2184-2190. |
| [14] | WANG Nianbin, HE Ming, WANG Hongbin, LANG Zeyu. Underwater target feature extraction method based on convolutional neural network [J]. Systems Engineering and Electronics, 2018, 40(6): 1197-1203. |
| [15] | YU Xiaohan, CHEN Xiaolong, HUANG Yong, GUAN Jian, HE You. Radar detection for moving target in short-time sparse fractional representative domain [J]. Systems Engineering and Electronics, 2018, 40(11): 2426-. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||