Systems Engineering and Electronics ›› 2021, Vol. 43 ›› Issue (12): 3614-3623.doi: 10.12305/j.issn.1001-506X.2021.12.24
• Systems Engineering • Previous Articles Next Articles
Research on effectiveness evaluation method of equipment system based on node importance and improved information entropy
Dongtao WEI1,2,*, Xiaodong LIU1, Peng LI2, Yujin CHEN1
- 1. College of Equipment Management and UAV Engineering, Air Force Engineering University, Xi'an 710051, China
2. Air Force Material and Four-Stations Department, Air Force Logistics College, Xuzhou 221000, China
-
Received:2021-01-12Online:2021-11-24Published:2021-11-30 -
Contact:Dongtao WEI
CLC Number:
Cite this article
Dongtao WEI, Xiaodong LIU, Peng LI, Yujin CHEN. Research on effectiveness evaluation method of equipment system based on node importance and improved information entropy[J]. Systems Engineering and Electronics, 2021, 43(12): 3614-3623.
share this article
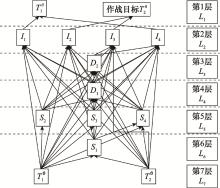
Table 2
The first-level decomposition results"
| 节点vi | 可达集R(vi) | 先行集B(vi) | R(vi)∩B(vi) |
| S1 | S1, S4, D1, D2, I1, I2, I3, I4, T1θ, T2θ | S1, T1ϑ, T2ϑ | S1 |
| S2 | S2, D1, D2, I1, I2, I3, I4, T1θ, T2θ | S2, T1ϑ | S2 |
| S3 | S3, D1, D2, I1, I2, I3, I4, T1θ, T2θ | S3, T1ϑ | S3 |
| S4 | S4, D1, D2, I1, I2, I3, I4, T1θ, T2θ | S1, S4, T1ϑ, T2ϑ | S4 |
| D1 | D1, D2, I1, I2, I3, I4, T1θ, T2θ | S1, S2, S3, S4, D1, T1ϑ, T2ϑ | D1 |
| D2 | D2, I3, I4, T1θ, T2θ | S1, S2, S3, S4, D1, D2, T1ϑ, T2ϑ | D2 |
| I1 | I1, T1θ | S1, S2, S3, S4, D1, I1, T1ϑ, T2ϑ | I1 |
| I2 | I2, T2θ | S1, S2, S3, S4, D1, I2, T1ϑ, T2ϑ | I2 |
| I3 | I3, T2θ | S1, S2, S3, S4, D1, D2, I3, T1ϑ, T2ϑ | I3 |
| I4 | I4, T1θ | S1, S2, S3, S4, D1, D2, I4, T1ϑ, T2ϑ | I4 |
| T1ϑ | S1, S2, S3, S4, D1, D2, I1, I2, I3, I4, T1ϑ, T1θ, T2θ | T1ϑ | T1ϑ |
| T1θ | T1θ | S1, S2, S3, S4, D1, D2, I1, I4, T1ϑ, T1θ, T2ϑ | T1θ |
| T2ϑ | S1, S4, D1, D2, I1, I2, I3, T1θ, T2ϑ, T2θ | T2ϑ | T2ϑ |
| T2θ | T2θ | S1, S2, S3, S4, D1, D2, I2, I3, T1ϑ, T2ϑ, T2θ | T2θ |
Table 3
Various weights of nodes"
| 节点 | 网络全局权重 | 节点强度 | 节点效率 | 网络局部权重 | 节点重要度 | 节点网络权重 |
| S1 | 0.091 8 | 1.6 | 0.294 9 | 0.947 4 | 0.087 0 | 0.087 0 |
| S2 | 0.071 6 | 1.0 | 0.294 9 | 0.647 4 | 0.046 4 | 0.046 4 |
| S3 | 0.071 6 | 1.0 | 0.294 9 | 0.647 4 | 0.046 4 | 0.046 4 |
| S4 | 0.128 6 | 1.4 | 0.359 0 | 0.879 5 | 0.113 1 | 0.113 1 |
| D1 | 0.344 5 | 3.0 | 0.384 6 | 1.692 3 | 0.583 0 | 0.583 0 |
| D2 | 0.258 4 | 2.0 | 0.230 8 | 1.115 4 | 0.288 2 | 0.288 2 |
| I1 | 0.212 1 | 1.0 | 0.076 9 | 0.538 5 | 0.114 2 | 0.114 2 |
| I2 | 0.212 1 | 1.0 | 0.076 9 | 0.538 5 | 0.114 2 | 0.114 2 |
| I3 | 0.231 4 | 1.0 | 0.076 9 | 0.538 5 | 0.124 6 | 0.124 6 |
| I4 | 0.231 4 | 1.0 | 0.076 9 | 0.538 5 | 0.124 6 | 0.124 6 |
| T1ϑ | 0.087 4 | 1.2 | 0.488 7 | 0.824 4 | 0.072 1 | 0.210 9 |
| T1θ | 0.231 4 | 1.2 | 0 | 0.6 | 0.138 8 | - |
| T2ϑ | 0.025 7 | 0.4 | 0 | 0.2 | 0.005 1 | 0.180 1 |
| T2θ | 0.231 4 | 1.2 | 0.312 8 | 0.756 4 | 0.175 0 | - |
Table 4
Equipment integrity and node weight"
| 节点 | 节点生存力 | 节点可靠性 | 装备完好度 | 节点权重 |
| S1 | 0.923 6 | 1.00 | 0.923 6 | 0.080 3 |
| S2 | 0.741 4 | 0.91 | 0.674 7 | 0.031 3 |
| S3 | 0.816 7 | 0.82 | 0.669 7 | 0.031 0 |
| S4 | 0.566 0 | 1.00 | 0.566 0 | 0.064 0 |
| D1 | 0.741 4 | 0.91 | 0.674 7 | 0.393 3 |
| D2 | 0.619 4 | 1.00 | 0.619 4 | 0.178 5 |
| I1 | 0.816 7 | 0.96 | 0.784 0 | 0.089 5 |
| I2 | 0.659 4 | 0.97 | 0.639 6 | 0.073 0 |
| I3 | 0.616 0 | 0.98 | 0.603 7 | 0.075 2 |
| I4 | 0.749 9 | 0.95 | 0.712 4 | 0.088 7 |
| T1 | 0.800 0 | 1.00 | 0.800 0 | 0.168 7 |
| T2 | 0.800 0 | 1.00 | 0.800 0 | 0.144 0 |
Table 5
Amount of self-information on the network side of operation loop"
| 名称 | T1-S1 | T1-S2 | T1-S3 | T2-S1 |
| E=f(vT, vS) | 0.638 3 | 0.756 7 | 0.517 3 | 0.496 2 |
| 自信息量 | 0.448 9 | 0.278 8 | 0.659 1 | 0.700 8 |
| 综合自信息量 | 0.006 1 | 0.001 5 | 0.003 4 | 0.008 1 |
| 名称 | S2-D1 | S3-D1 | S4-D1 | S4-D2 |
| E=f(vS, vD) | 0.856 1 | 0.661 9 | 0.768 5 | 0.801 2 |
| 自信息量 | 0.155 4 | 0.412 6 | 0.263 3 | 0.221 6 |
| 综合自信息量 | 0.001 9 | 0.005 | 0.006 6 | 0.002 5 |
| 名称 | D1-I1 | D1-I2 | D2-I3 | D2-I4 |
| E=f(vD, vI) | 0.782 1 | 0.654 1 | 0.785 6 | 0.831 4 |
| 自信息量 | 0.245 8 | 0.424 5 | 0.241 3 | 0.184 6 |
| 综合自信息量 | 0.008 7 | 0.012 2 | 0.003 2 | 0.002 9 |
| 名称 | I1-T1 | I2-T2 | I3-T2 | I4-T1 |
| E=f(vI, vT) | 0.645 2 | 0.774 9 | 0.599 8 | 0.810 6 |
| 自信息量 | 0.438 2 | 0.255 0 | 0.511 2 | 0.210 0 |
| 综合自信息量 | 0.006 6 | 0.002 7 | 0.005 5 | 0.003 1 |
| 名称 | S1-S4 | D1-D2 | - | - |
| E=f(vI, vI)/E=f(vD, vD) | 0.786 3 | 0.858 2 | - | - |
| 自信息量 | 0.240 4 | 0.152 9 | - | - |
| 综合自信息量 | 0.001 2 | 0.010 7 | - | - |
Table 6
Target node operation loop and its uncertain self-information amount"
| 目标 | 编号 | 作战环 | 不确定性自信息量 |
| T1 | 1 | T1-S1-S4-D2-I4-T1 | 0.015 8 |
| 2 | T1-S1-S4-D1-D2-I4-T1 | 0.030 6 | |
| 3 | T1-S1-S4-D1-I1-T1 | 0.029 2 | |
| 4 | T1-S2-D1-I1-T1 | 0.018 7 | |
| 5 | T1-S2-D1-D2-I4-T1 | 0.020 1 | |
| 6 | T1-S3-D1-I1-T1 | 0.025 3 | |
| 7 | T1-S3-D1-D2-I4-T1 | 0.025 1 | |
| T2 | 1 | T2-S1-S4-D2-I3-T2 | 0.020 5 |
| 2 | T2-S1-S4-D1-I2-T2 | 0.030 8 | |
| 3 | T2-S1-S4-D1-D2-I3-T2 | 0.035 3 |
| 1 | 于芹章, 张英朝, 张静, 等. 基于整体效果的装备体系作战效能评估方法研究[J]. 系统仿真技术, 2011, 7 (3): 183- 189. |
| YU Q Z , ZHANG Y C , ZHANG J , et al. Research on combat effectiveness evaluation method of equipment system based on o verall effect[J]. System Simulation Technology, 2011, 7 (3): 183- 189. | |
| 2 | 张送保, 张维明, 刘忠, 等. 复杂体系效能测度建模研究[J]. 系统工程学报, 2007, 13 (7): 515- 519. |
| ZHANG S B , ZHANG W M , LIU Z , et al. Research on modeling of complex system effectiveness measurement[J]. Journal of Systems Engineering, 2007, 13 (7): 515- 519. | |
| 3 | 马力, 张明智. 网络化体系效能评估建模研究[J]. 军事运筹与系统工程, 2016, 30 (1): 12- 17. |
| MA L , ZHANG M Z . Research on effectiveness evaluation modeling of networked system[J]. Military Operations Research and Systems Engineering, 2016, 30 (1): 12- 17. | |
| 4 |
谭跃进, 张小可, 杨克巍. 武器装备体系网络化描述与建模方法[J]. 系统管理学报, 2012, 21 (6): 781- 786.
doi: 10.3969/j.issn.1005-2542.2012.06.009 |
|
TAN Y J , ZHANG X K , YANG K W . Networked description and modeling method of weapon equipment system[J]. Journal of Systems Management, 2012, 21 (6): 781- 786.
doi: 10.3969/j.issn.1005-2542.2012.06.009 |
|
| 5 | 卜广志. 基于信息流的武器装备体系效能模型[J]. 火力与指挥控制, 2009, 34 (8): 34- 37. |
| BU G Z . Weapon equipment system effectiveness model based on information flow[J]. Fire Power and Command Control, 2009, 34 (8): 34- 37. | |
| 6 | 罗承昆, 陈云翔, 王莉莉, 等. 基于作战环和改进信息熵的体系效能评估方法[J]. 系统工程与电子技术, 2019, 41 (1): 73- 80. |
| LUO C K , CHEN Y X , WANG L L , et al. System effectiveness evaluation method based on combat loop and improved information entropy[J]. Systems Engineering and Electronics, 2019, 41 (1): 73- 80. | |
| 7 | 梁家林, 熊伟. 基于作战环的武器装备体系能力评估方法[J]. 系统工程与电子技术, 2019, 41 (8): 1810- 1819. |
| LIANG J L , XIONG W . Weapon system capability evaluation method based on combat ring[J]. Systems Engineering and Electronics, 2019, 41 (8): 1810- 1819. | |
| 8 | 周琛, 尚柏林, 宋笔锋, 等. 基于作战环的航空武器装备体系贡献率评估[EB/OL]. [2021-01-10]. http://kns.cnki.net/kcms/detail/11.1929.V.20201214.1727.006.html. |
| ZHOU C, SHANG B L, SONG B F, et al. Assessment of contribution rate of aviation weapon equipment system based on combat loop[EB/OL]. [2021-01-10]. http://kns.cnki.net/kcms/detail/11.1929.V.20201214.1727.006.html. | |
| 9 | 吴坚, 郭齐胜, 于桓凯. 基于ISM的作战活动模型的结构分析方法研究[J]. 装备指挥技术学院学报, 2011, 22 (5): 118- 122. |
| WU J , GUO Q S , YU H K . Research on structural analysis method of combat activity model based on ISM[J]. Journal of t he Academy of Equipment Command & Technology, 2011, 22 (5): 118- 122. | |
| 10 | 刘伟强, 徐立云. 基于ISM和复杂网络的制造系统关键脆性因子辨识[EB/OL]. [2021-01-10]. http://kns.cnki.net/kcms/detail/11.5946.TP.20201126.1022.006.html. |
| LIU W Q, XU L Y. Identification of key fragility factors of manufacturing system based on ISM and complex network[EB/OL]. [2021-01-10]. http://kns.cnki.net/kcms/detail/11.5946.TP.20201126.1022.006.html. | |
| 11 | 郑世明, 王洪军, 孙涛. 基于ISM的作战仿真模型体系结构建模[J]. 指挥控制与仿真, 2016, 38 (1): 23- 27. |
| ZHENG S M , WANG H J , SUN T . ISM-based combat simulation model architecture modeling[J]. Command Control and Simulation, 2016, 38 (1): 23- 27. | |
| 12 | 商慧琳. 武器装备体系作战网络建模及能力评估方法研究[D]. 长沙: 国防科学技术大学, 2013. |
| SHANG H L. Research on modeling and capability evaluation method of weapon equipment system combat network[D]. Changsha: National University of Defense Technology, 2013. | |
| 13 | 张明智, 马力. 体系对抗OODA循环鲁棒性建模及仿真分析[J]. 系统仿真学报, 2017, 29 (9): 1968- 1976. |
| ZHANG M Z , MA L . Robustness modeling and simulation analysis of system against OODA cycle[J]. Journal of System Simulation, 2017, 29 (9): 1968- 1976. | |
| 14 | 徐文超, 薛青, 于屏岗, 等. 作战系统网络化建模方法研究[J]. 系统仿真学报, 2014, 26 (9): 2142- 2147. |
| XU W C , XUE Q , YU P G , et al. Research on network modeling method of combat system[J]. Journal of System Simulation, 2014, 26 (9): 2142- 2147. | |
| 15 | 段佳勇, 郑宏达. 基于节点重要度的复杂网络脆弱性分析方法[J]. 控制工程, 2020, 27 (4): 692- 696. |
| DUAN J Y , ZHENG H D . Complex network vulnerability analysis method based on node importance[J]. Control Engineering, 2020, 27 (4): 692- 696. | |
| 16 | 周漩, 张凤鸣, 周卫平, 等. 利用节点效率评估复杂网络功能鲁棒性[J]. 物理学报, 2012, 61 (19): 190201. |
| ZHOU X , ZHANG F M , ZHOU W P , et al. Using node efficiency to evaluate the functional robustness of complex networks[J]. Acta Physica Sinica, 2012, 61 (19): 190201. | |
| 17 | 陈春良, 昝翔, 张仕新, 等. 基于多维关系复杂网络的装备重要度评估方法[J]. 兵工学报, 2017, 38 (6): 1168- 1177. |
| CHEN C L , ZAN X , ZHANG S X , et al. Equipment importance evaluation method based on complex network of multi-dimensional relationships[J]. Acta Armamentarii, 2017, 38 (6): 1168- 1177. |
| [1] | Yingqi LU, Chengli FAN, Qiang FU, Xiaowen ZHU, Wei LI. Missile defense target threat assessment based on improved similarity measure and information entropy of IFRS [J]. Systems Engineering and Electronics, 2022, 44(4): 1230-1238. |
| [2] | Xinping MI, Xihong CHEN, Zan LIU, Yongjin LIU, Qiang LIU. Bispectrum feature recognition of radar signal based on entropy evaluation and modal decomposition [J]. Systems Engineering and Electronics, 2021, 43(8): 2116-2123. |
| [3] | Chen ZHOU, Bifeng SONG, Bolin SHANG, Yaozu WANG, Erqin KE. System of systems contribution rate evaluation based on operational network reliability [J]. Systems Engineering and Electronics, 2021, 43(7): 1875-1883. |
| [4] | Weisheng YANG, Yu WANG, Yang YANG, Liang TANG. Combat network effectiveness evaluation under different node attack strategies based on operation loop [J]. Systems Engineering and Electronics, 2021, 43(11): 3220-3228. |
| [5] | Leilei ZHANG, Long XIE, Xu GAO, Tianyu SUN, Feng ZHANG. Research on synthetic reliability assessment method for high-value ammunition [J]. Systems Engineering and Electronics, 2021, 43(11): 3399-3404. |
| [6] | Henglu LI, Baixiao CHEN, Yi DING, Zhaoming ZHANG. Nearest neighbor data association algorithm based on information entropy weight [J]. Systems Engineering and Electronics, 2020, 42(4): 806-812. |
| [7] | Zhenshuo LEI, Songtao LIU, Yang GE, Zhenming WEN. Parameter selection and feature representation method of jamming effect online evaluation [J]. Systems Engineering and Electronics, 2020, 42(12): 2755-2760. |
| [8] | Chen LI, Jun'an YANG, Hui LIU. Modulation recognition algorithm based on information entropy and GA-ELM [J]. Systems Engineering and Electronics, 2020, 42(1): 223-229. |
| [9] | LIU Peng, ZHAO Danling, TAN Yuejin, YANG Kewei, DOU Yajie. Multi-task oriented contribution evaluation method of weapon equipment system of systems [J]. Systems Engineering and Electronics, 2019, 41(8): 1763-1770. |
| [10] | LIANG Jialin, XIONG Wei. Capabilities assessment of the weaponry system based on combat ring [J]. Systems Engineering and Electronics, 2019, 41(8): 1810-1819. |
| [11] | YANG Kewei, YANG Zhiwei, TAN Yuejin, ZHAO Qingsong. Review of the evaluation methods of equipment system of systems facing the contribution rate [J]. Systems Engineering and Electronics, 2019, 41(2): 311-321. |
| [12] | LUO Chengkun, CHEN Yunxiang, WANG Lili, WANG Zezhou, CHANG Zheng. Effectiveness evaluation method of system-of-systems based on operation loop and improved information entropy [J]. Systems Engineering and Electronics, 2019, 41(1): 73-80. |
| [13] | ZHAO Danling, TAN Yuejin, LI Jichao, XIA Boyuan, DOU Yajie, JI Shengping. Armament system of systems contribution evaluation based on operation loop [J]. Systems Engineering and Electronics, 2017, 39(10): 2239-2247. |
| [14] | LUO Kai, ZHANG Ming-zhi, WU Xi. Key nodes analysis model for space information temporal network based on operation loop [J]. Systems Engineering and Electronics, 2016, 38(7): 1572-1576. |
| [15] | ZHANG Qiang, LI Jianhua, SHEN Di, MA Chuang. Research on network modeling and optimization of#br# operation system of systems based on complex network [J]. Systems Engineering and Electronics, 2015, 37(5): 1066-1071. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||