Systems Engineering and Electronics ›› 2021, Vol. 43 ›› Issue (9): 2373-2382.doi: 10.12305/j.issn.1001-506X.2021.09.01
• Electronic Technology • Next Articles
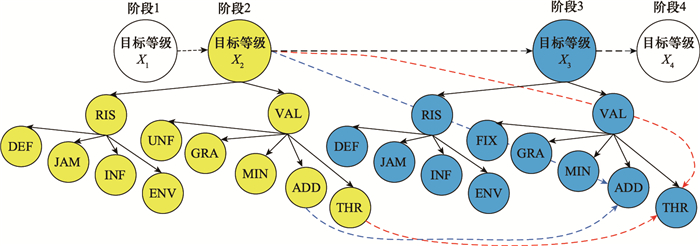
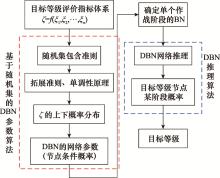
Method of electronic countermeasure targets' list generation based on RS-DBN
Luda ZHAO*, Bin WANG
- College of Electronics Engineering of National University of Defence Technology, Hefei 230037, China
-
Received:2020-09-14Online:2021-08-20Published:2021-08-26 -
Contact:Luda ZHAO
CLC Number:
Cite this article
Luda ZHAO, Bin WANG. Method of electronic countermeasure targets' list generation based on RS-DBN[J]. Systems Engineering and Electronics, 2021, 43(9): 2373-2382.
share this article
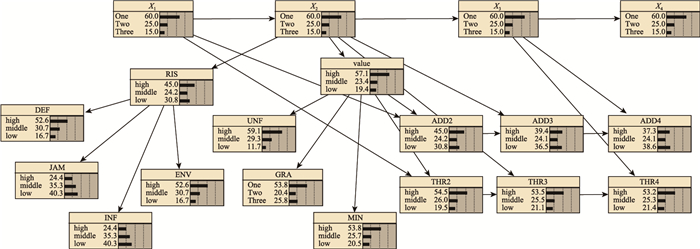
Table 1
Node state space in DBN"
| 节点 | 状态空间 | 状态字母代号 |
| 目标等级 | {一级, 二级, 三级} | {One, Two, Three} |
| RIS | {高, 中, 低} | {High, Middle, Low} |
| VAL | {高, 中, 低} | {High, Middle, Low} |
| DEF | {高, 中, 低} | {High, Middle, Low} |
| JAM | {高, 中, 低} | {High, Middle, Low} |
| INF | {高, 中, 低} | {High, Middle, Low} |
| ENV | {高, 中, 低} | {High, Middle, Low} |
| UNF | {高, 中, 低} | {High, Middle, Low} |
| GRA | {一级, 二级, 三级} | {One, Two, Three} |
| MIN | {高, 中, 低} | {High, Middle, Low} |
| ADD | {高, 中, 低} | {High, Middle, Low} |
| THR | {高, 中, 低} | {High, Middle, Low} |
Table 1
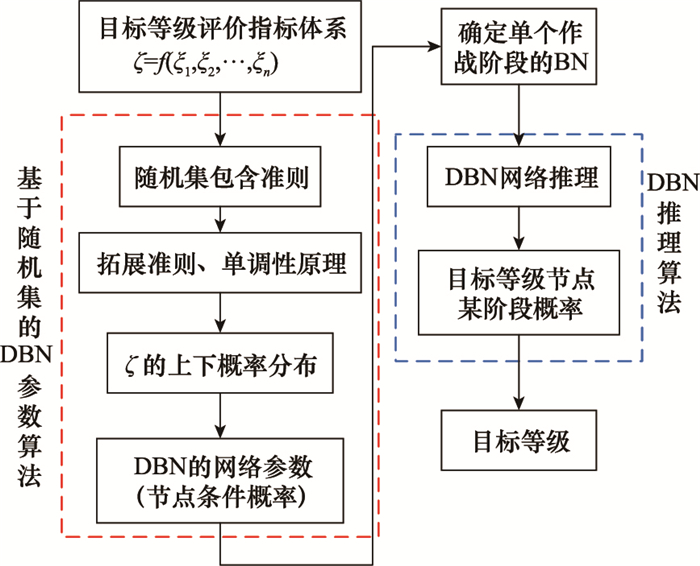
Table 4
Node CPT 3 %"
| value | P(UNF | value) | P(GRA | value) | P(MIN | value) | P(THR | value) | ||||||||||||
| high | middle | low | One | Two | Three | high | middle | low | high | middle | low | |||||
| high | 66.56 | 24.56 | 8.88 | 60 | 20 | 20 | 60 | 30 | 10 | 61.25 | 22.43 | 16.32 | ||||
| middle | 45.457 | 45.567 | 8.976 | 50 | 20 | 30 | 50 | 20 | 30 | 18.88 | 29.56 | 51.56 | ||||
| low | 53.45 | 23.45 | 23.1 | 40 | 22 | 38 | 40 | 20 | 40 | 23.67 | 22.18 | 54.15 | ||||
Table 4
Table 5
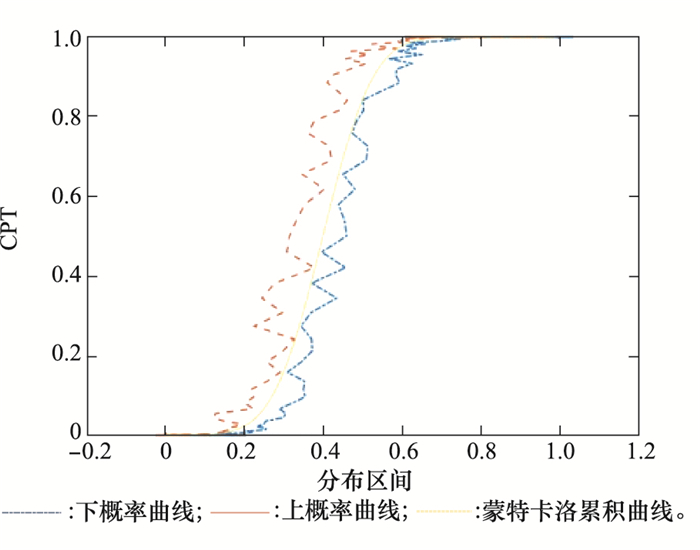
Interval probability assignment table of ξJAM, ξENV"
| 划分区间 | [0, 0.1) | [0.1, 0.2) | [0.2, 0.3) | [0.3, 0.4) | [0.4, 0.5) | [0.5, 0.6) | [0.6, 0.7) | [0.7, 0.8) | [0.8, 0.9) | [0.9, 1.0] |
| ξJAM | 0.004 18 | 0.003 26 | 0.002 29 | 0.001 31 | 0.000 30 | 0.000 71 | 0.001 71 | 0.002 68 | 0.003 63 | 0.004 54 |
| ξENV | 0.134 92 | 0.116 71 | 0.100 97 | 0.087 34 | 0.075 56 | 0.065 37 | 0.056 55 | 0.048 92 | 0.042 32 | 0.036 61 |
Table 5
| 1 | 刘庆国. 电子对抗作战指挥系统研究[M]. 北京: 国防大学出版社, 2011. |
| LIU Q G . Research on electronic countermeasures operational command system[M]. Beijing: National Defense University Press, 2011. | |
| 2 | 奚之飞, 徐安, 寇英信, 等. 基于灰主成分的空战目标威胁评估[J]. 系统工程与电子技术, 2021, 43 (1): 147- 155. |
| XI Z F , XU A , KOU Y X , et al. Air combat target threat assessment based on gray principal component[J]. System Engineering and Electronic Technology, 2021, 43 (1): 147- 155. | |
| 3 | ZHANG K, LIU P P, LI K, et al. Multi-target threat assessment in air combat based on AHP and FVIKOR[C]//Proc. of the IEEE International Conference on Unmanned Systems, 2017. |
| 4 | 奚之飞, 徐安, 寇英信, 等. 基于前景理论的空战目标威胁评估[J]. 兵工学报, 2020, 41 (6): 1236- 1248. |
| XI Z F , XU A , KOU Y X , et al. Threat evaluation of air combat targets based on prospect theory[J]. Acta Armamentarii, 2020, 41 (6): 1236- 1248. | |
| 5 | XU X M, YANG R N, YANG Y. Threat assessment in air combat based on elm neural network[C]//Proc. of the IEEE International Conference on Artificial Intelligence and Computer Applications, 2019. |
| 6 | ZHANG S L, ZHANG T, XU X M. Threat estimation of aerial target based on extreme learning machine[C]//Proc. of the Chinese Control Conference, 2019. |
| 7 | 张永利, 潘哲, 刘楠楠. 基于离散Hopfield神经网络的辐射源目标威胁估计[J]. 指挥信息系统与技术, 2020, 11 (2): 39- 43, 48. |
| ZHANG Y L , PAN Z , LIU N N . The threat estimation of radiation source target based on discrete Hopfield neural network[J]. Command Information System and Technology, 2020, 11 (2): 39- 43, 48. | |
| 8 |
SUN H W , XIE X F . Threat evaluation method of warships formation air defense based on AR(p)-DITOPSIS[J]. Journal of Systems Engineering and Electronics, 2019, 30 (2): 297- 307.
doi: 10.21629/JSEE.2019.02.09 |
| 9 |
侯思尧, 李永光, 陈思静, 等. 利用主客观集成赋权法的多目标威胁评估[J]. 电讯技术, 2019, 59 (8): 956- 961.
doi: 10.3969/j.issn.1001-893x.2019.08.016 |
|
HOU S Y , LI Y G , CHEN S J , et al. Multi-target threat assessment using subjective and objective integrated weightingmethod[J]. Telecommunication Technology, 2019, 59 (8): 956- 961.
doi: 10.3969/j.issn.1001-893x.2019.08.016 |
|
| 10 |
FENG J F , ZHANG Q , HU J H , et al. Dynamic assessment method of air target threat based on improved GIFSS[J]. Journal of Systems Engineering and Electronics, 2019, 30 (3): 525- 534.
doi: 10.21629/JSEE.2019.03.10 |
| 11 |
刘昊, 邢岩, 吴世杰. 基于体系破击的联合火力打击目标价值评估[J]. 系统工程与电子技术, 2020, 42 (12): 2802- 2810.
doi: 10.3969/j.issn.1001-506X.2020.12.17 |
|
LIU H , XING Y , WU S J . Value evaluation of joint fire strike target based on system destruction[J]. System Engineering and Electronics, 2020, 42 (12): 2802- 2810.
doi: 10.3969/j.issn.1001-506X.2020.12.17 |
|
| 12 | 汪鑫, 龙光正, 汪志宏, 等. 基于灰色聚类和序关系的防空保卫目标排序研究[J]. 弹箭与制导学报, 2018, 38 (2): 25- 29. |
| WANG X , LONG G Z , WANG Z H , et al. Research on air defense target sequencing based on grey clustering and order relation[J]. Journal of Projectiles and Guidance, 2018, 38 (2): 25- 29. | |
| 13 | 孙海文, 谢晓方, 孙涛, 等. 小样本数据缺失状态下DBN舰艇编队防空目标威胁评估方法[J]. 系统工程与电子技术, 2019, 41 (6): 1300- 1308. |
| SUN H W , XIE X F , SUN T , et al. The threat assessment method of DBN fleet air defense targets under the state of small sample data missing[J]. System Engineering and Electronics, 2019, 41 (6): 1300- 1308. | |
| 14 | WANG X , ZUO J Z , YANG R N , et al. Target threat assessment based on dynamic bayesian network[J]. Journal of Physics: Conference Series, 2019, 1302 (4): 042023. |
| 15 |
MA S D , ZHANG H Z , YANG G Q . Target threat level assessment based on cloud model under fuzzy and uncertain conditions in air combat simulation[J]. Aerospace Science and Technology, 2017, 67, 49- 53.
doi: 10.1016/j.ast.2017.03.033 |
| 16 |
陈怀进, 刘雅奇, 和伟, 等. 基于DBN的雷达干扰目标选择方法[J]. 现代雷达, 2014, 36 (9): 6- 10.
doi: 10.3969/j.issn.1004-7859.2014.09.002 |
|
CHEN H J , LIU Y Q , HE W , et al. The method of radar jamming target selection based on DBN[J]. Modern Radar, 2014, 36 (9): 6- 10.
doi: 10.3969/j.issn.1004-7859.2014.09.002 |
|
| 17 | MENG G L, ZHOU M Z, ZHANG H M, et al. Threat assessment for rotte based on cooperative tactical recognition[C]//Proc. of the IEEE International Conferences on Ubiquitous Computing & Communications and Data Science and Computational Intelligence and Smart Computing, Networking and Services, 2019. |
| 18 | XU Y H, CHENG S Y, ZHANG H B, et al. Air target combat intention identification based on IE-DSBN[C]//Proc. of the International Workshop on Electronic Communication and Artificial Intelligence, 2020. |
| 19 | 全军军事委员会. 中国人民解放军军语[M]. 北京: 军事科学出版社, 2011. |
| Military Committee of the Army . Military Language of the Chinese People's Liberation Army[M]. Beijing: Military Science Press, 2011. | |
| 20 |
张明双, 徐克虎, 李灵之. 合成旅目标威胁评估指标体系[J]. 火力与指挥控制, 2019, 44 (12): 108- 113.
doi: 10.3969/j.issn.1002-0640.2019.12.022 |
|
ZHANG M S , XU K H , LI L Z . Synthetic brigade target threat assessment index system[J]. Fire Power & Command Control, 2019, 44 (12): 108- 113.
doi: 10.3969/j.issn.1002-0640.2019.12.022 |
|
| 21 | DZIADOSZ A, BANACH D, MESZEK W, et al. Impact of the adopted strategy on the result of multi-criteria analysis of technology solution based on AHP (BOCR)[C]//Proc. of the MATEC Web of Conferences, 2018. |
| 22 | 李世楷. 随机集与集值鞅[M]. 贵阳: 贵州科技出版社, 1994. |
| LI S K . Random set and set-valued martingale[M]. Guiyang: Guizhou Science and Technology Press, 1994. | |
| 23 | DUBOIS D , HENRI P . A set-theoretic view of belief functions[J]. Classic Works of the Dempster-Shafer Theory of Belief Functions, 2008, 12, 375- 410. |
| 24 |
WANG L , WANG X S , YU J Z . Quasi-shadowing property on random partially hyperbolic sets[J]. Acta Mathematica Sinica, 2018, 34 (9): 1429- 1444.
doi: 10.1007/s10114-018-7314-4 |
| 25 | YANG J B , XU D L . Evidential reasoning rule for evidence combination[J]. Artificial Intelligence, 2013, 20 (5): 1- 29. |
| 26 | DU Y W , WANG Y M , QIN M . New evidential reasoning rule with both weight and reliability for evidence combination[J]. Computers & Industrial Engineering, 2018, 124, 493- 508. |
| 27 | GOODMAN I R , MAHLER R P , NGUYEN H T . Mathema-tics of data fusion[M]. Berlin: Springer Netherlands, 1997. |
| 28 | 邵国培, 曹志耀, 何俊. 电子对抗作战效能分析原理[M]. 北京: 军事科学出版社, 2013. |
| SHAO G P , CAO Z Y , HE J . Principles of effectiveness analysis of electronic countermeasures[M]. Beijing: Military Science Press, 2013. | |
| 29 | 冯泽彪, 汪建均, 马义中. 基于多变量高斯过程模型的贝叶斯建模与稳健参数设计[J]. 系统工程理论与实践, 2020, 40 (3): 703- 713. |
| FENG Z B , WANG J J , MA Y Z . Bayesian modeling and robust parameter design based on multivariable Gaussian process model[J]. System Engineering Theory and Practice, 2020, 40 (3): 703- 713. | |
| 30 |
AKINORI H , KENJI W , TAKIO K . Sparse discriminant analysis based on estimation of posterior probabilities[J]. Journal of Applied Statistics, 2019, 46 (15): 2761- 2785.
doi: 10.1080/02664763.2019.1613348 |
| 31 | SPRENT P , SMEETON N C . Applied nonparametric statistical methods[M]. Boca Raton: CRC press, 2016. |
| [1] | Jiabei CHEN, Qingping WANG, Yuan YE, Weiwei WU, Naichang YUAN. Analysis on wave-front phase distortion characteristics based on NSGA-Ⅱ [J]. Systems Engineering and Electronics, 2022, 44(5): 1439-1446. |
| [2] | Wenbo GUO, Changqing SONG, Yidan ZHANG, Hongzhi ZHAO, Shihai SHAO, Youxi TANG. Experimental testbed of self-interference suppression in electromagnetic spectrum umbrella [J]. Systems Engineering and Electronics, 2021, 43(9): 2637-2641. |
| [3] | Xiaozhou CHEN, Qingjun XING, Lidong ZHANG. Slow-time-frequency-modulation jamming method forSTAP airborne early-warning radar [J]. Systems Engineering and Electronics, 2021, 43(11): 3177-3184. |
| [4] | Bokai ZHANG, Weigang ZHU. Construction and key technologies of cognitive jamming decision-making system against MFR [J]. Systems Engineering and Electronics, 2020, 42(9): 1969-1975. |
| [5] | Bokai ZHANG, Weigang ZHU. DQN based decision-making method of cognitive jamming against multifunctional radar [J]. Systems Engineering and Electronics, 2020, 42(4): 819-825. |
| [6] | Guanglei MENG, Mingzhe ZHOU, Haiyin PIAO, Huimin ZHANG. Threat assessment method of dual-aircraft formation based on cooperative tactical recognition [J]. Systems Engineering and Electronics, 2020, 42(10): 2285-2293. |
| [7] | NIU Liqiang, XIE Yongjun, ZHANG Chungang, WU Dongwei. Detection simulation of AEGIS combat system for ballistic missile in electronic warfare environment [J]. Systems Engineering and Electronics, 2019, 41(6): 1195-1201. |
| [8] | SUN Haiwen, XIE Xiaofang, SUN Tao, ZHANG Longjie. Threat assessment method of warships formation air defense based on DBN under the condition of small sample data missing [J]. Systems Engineering and Electronics, 2019, 41(6): 1300-1308. |
| [9] | XING Qiang, ZHU Weigang, JIA Xin, ZHENG Guangyong. Jamming decision under condition of unknown jamming rule base [J]. Systems Engineering and Electronics, 2019, 41(2): 298-303. |
| [10] | ZHANG Huan, YANG Rennong, WU Jun, LI Qiuni, FU Xiuzhu, SUN Changyue. Research on multi-aircraft cooperative suppressing jamming embattling in electronic warfare planning [J]. Systems Engineering and Electronics, 2017, 39(3): 542-548. |
| [11] | YUE Kui-zhi, JIA Zhong-hu, JI Jin-zu, SU Min. Numerical simulation on the RCS of carrier based electronic warfare aircraft [J]. Systems Engineering and Electronics, 2014, 36(5): 852-858. |
| [12] | GAO Xiao-guang, LI Qing-yuan, DI Ruo-hai. MPC three dimensional dynamic path planning for UAV based on DBN threat assessment [J]. Systems Engineering and Electronics, 2014, 36(11): 2199-2205. |
| [13] | GE Shun, XIA Xue-zhi. DSBN used for recognition of tactical intention [J]. Systems Engineering and Electronics, 2014, 36(1): 76-83. |
| [14] | . Situation assessment using variable structure interval probability dynamic Bayesian network [J]. Systems Engineering and Electronics, 2013, 35(9): 1891-1897. |
| [15] | REN Jia, GAO Xiao-guang, BAI Yong. Discrete dynamic BN parameter learning under small sample and incomplete information [J]. Journal of Systems Engineering and Electronics, 2012, 34(8): 1723-1728. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||