Systems Engineering and Electronics ›› 2025, Vol. 47 ›› Issue (12): 4212-4224.doi: 10.12305/j.issn.1001-506X.2025.12.33
• Communications and Networks • Previous Articles
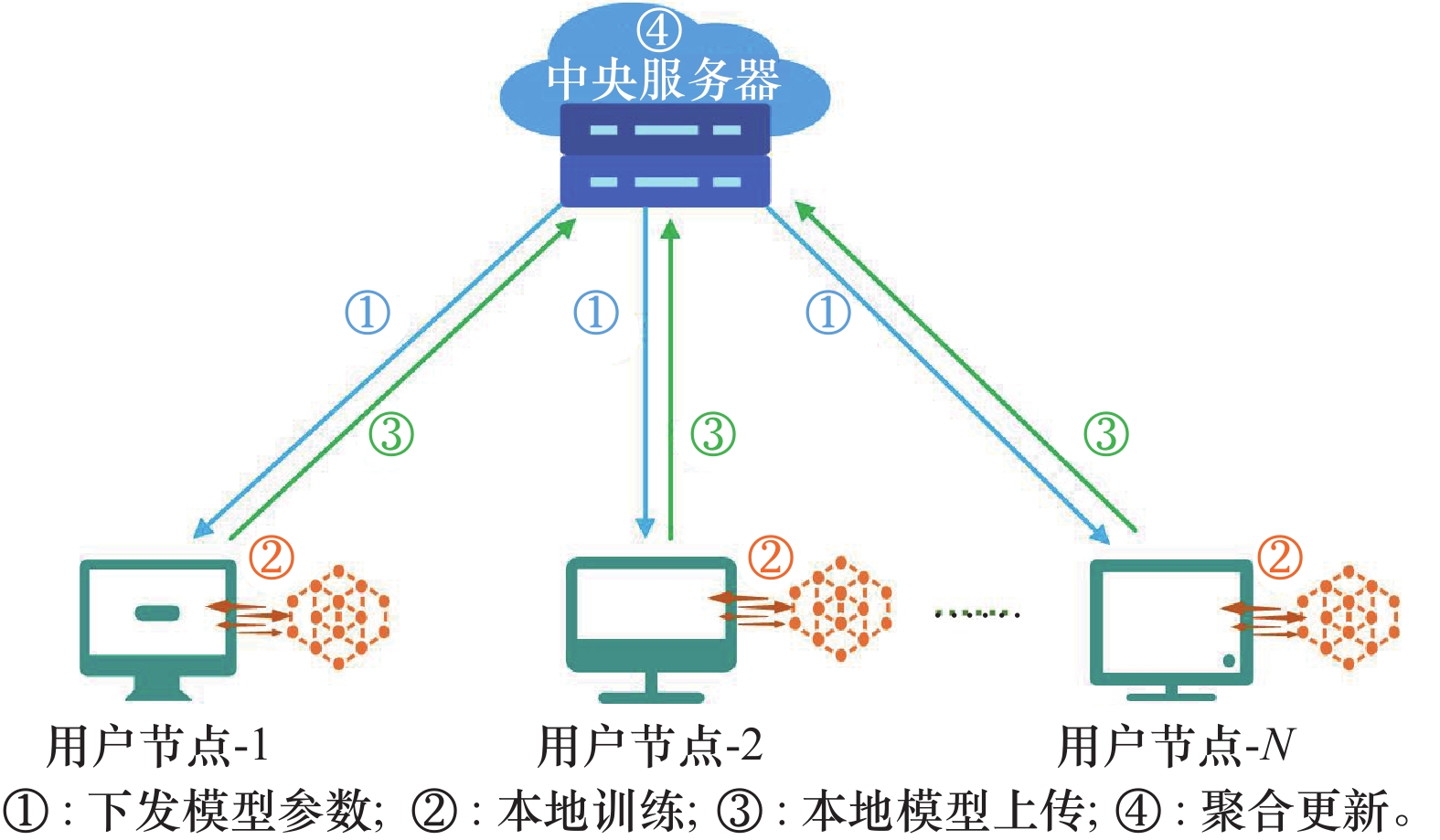
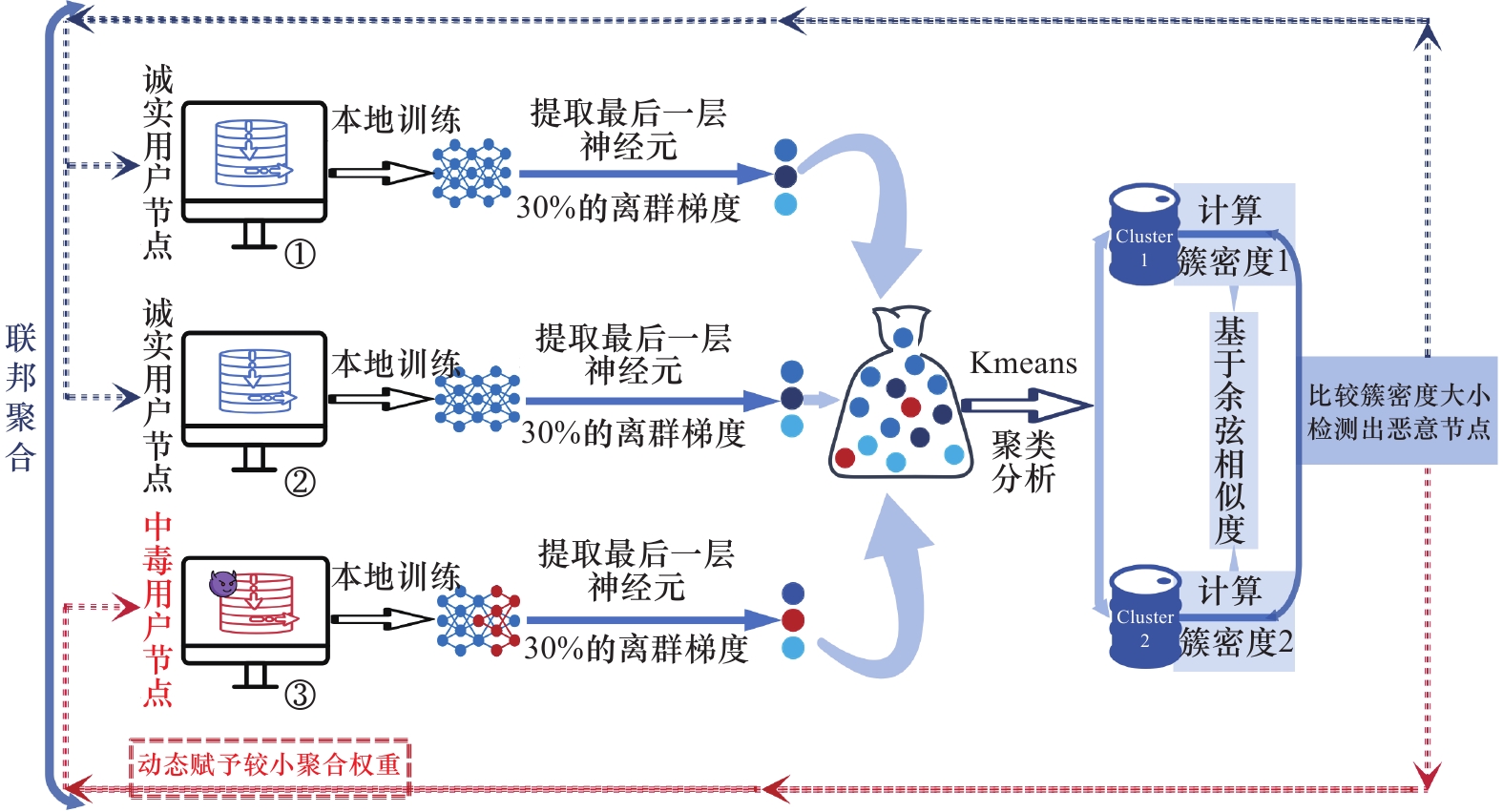
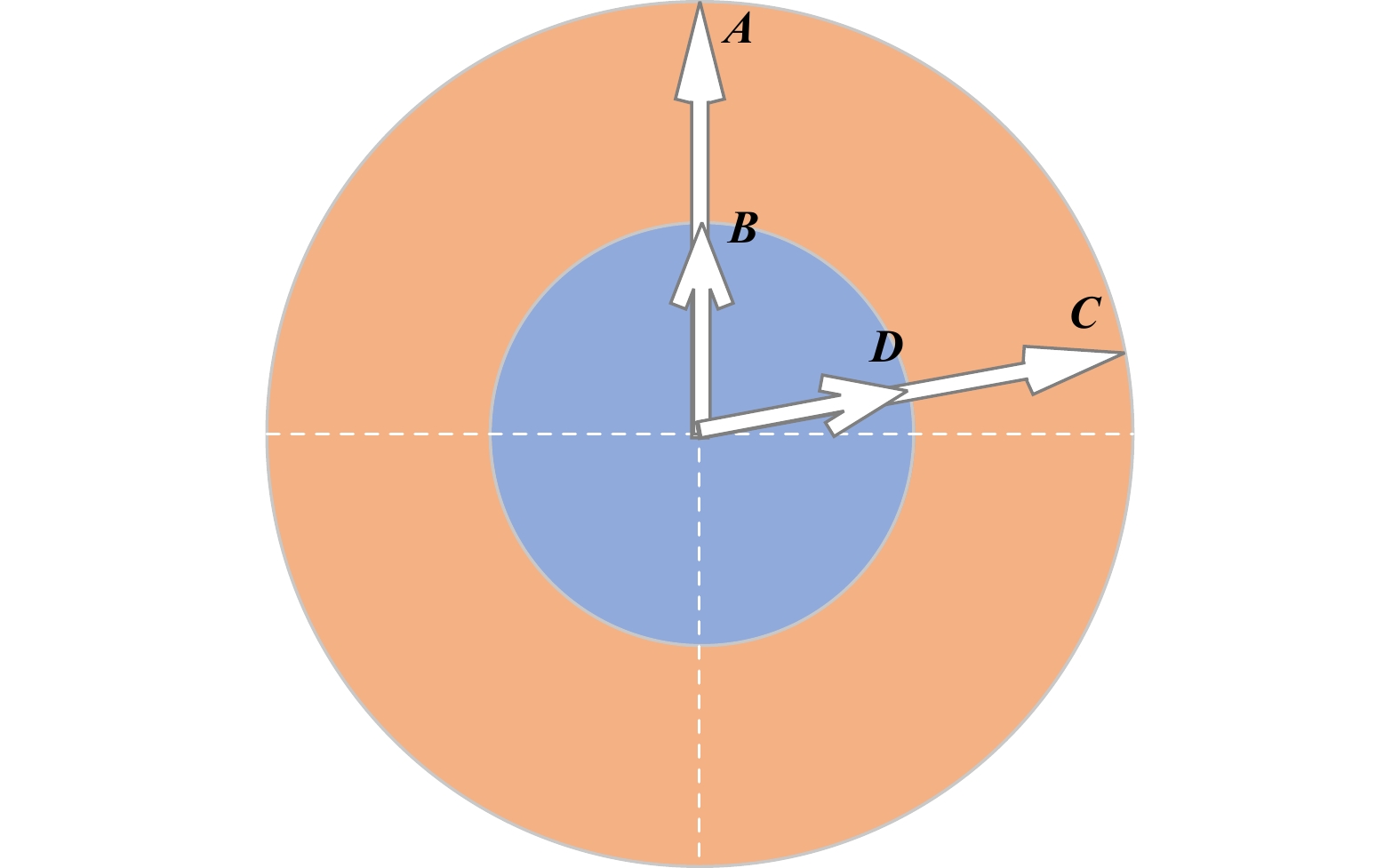
Security defense strategies for federated learning based on data poisoning attacks
Yangcheng MOU( ), Aiwang CHEN, Guirong CHEN, Jiming XU, Xiaomei YAN, Lian DUAN
), Aiwang CHEN, Guirong CHEN, Jiming XU, Xiaomei YAN, Lian DUAN
- School of Information and Navigation,Air Force Engineering University,Xi’an 710077,China
-
Received:2024-11-20Revised:2025-01-22Online:2025-05-23Published:2025-05-23 -
Contact:Aiwang CHEN E-mail:13170308389@163.com
CLC Number:
Cite this article
Yangcheng MOU, Aiwang CHEN, Guirong CHEN, Jiming XU, Xiaomei YAN, Lian DUAN. Security defense strategies for federated learning based on data poisoning attacks[J]. Systems Engineering and Electronics, 2025, 47(12): 4212-4224.
share this article
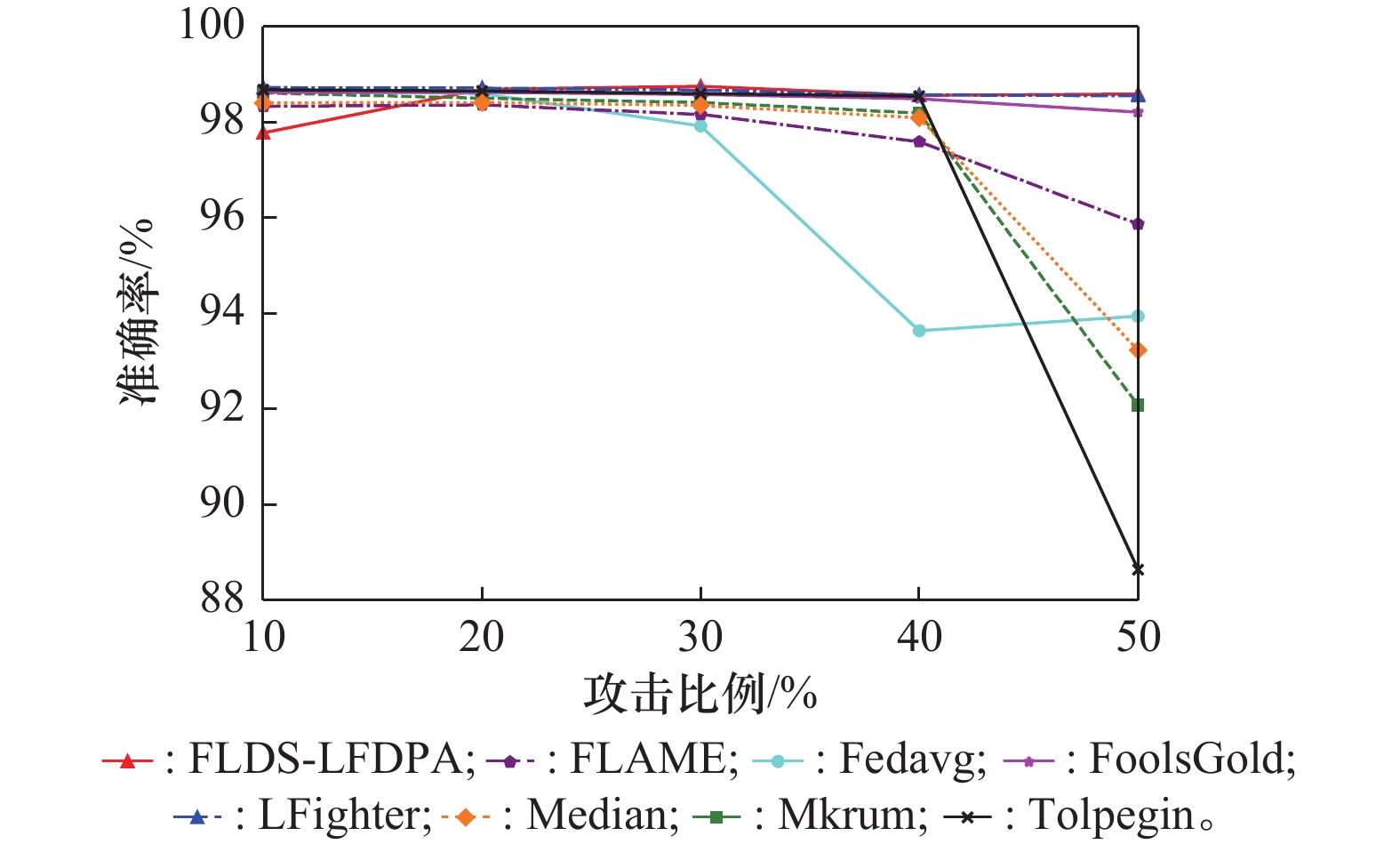
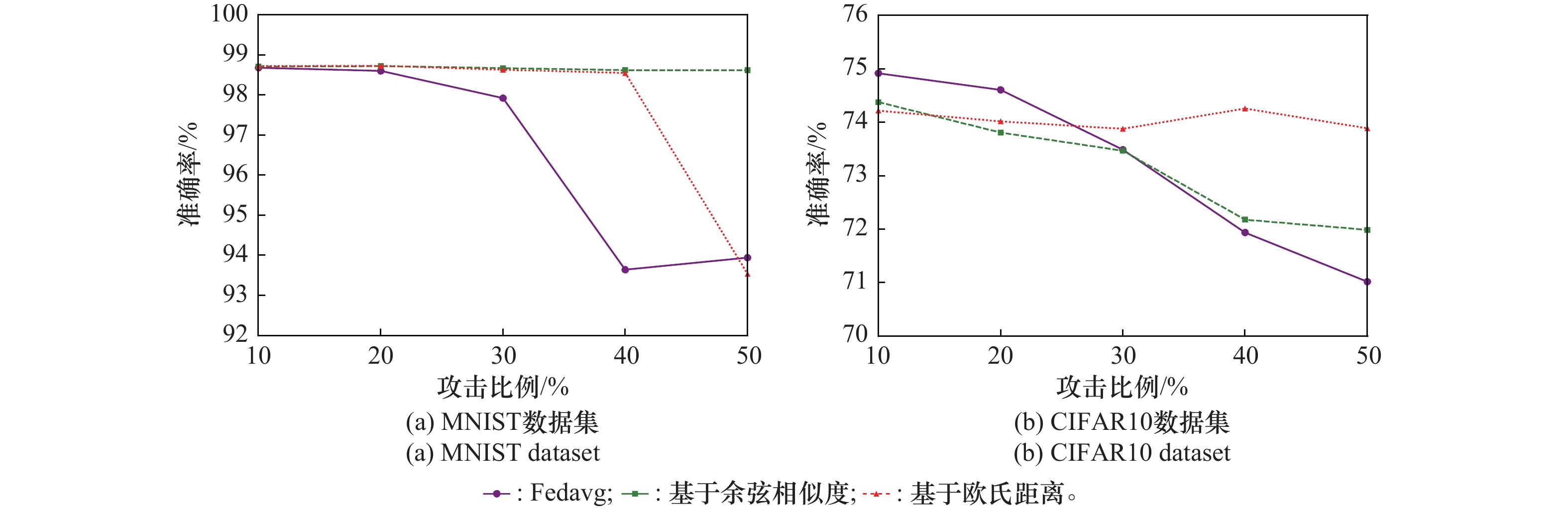
Table 1
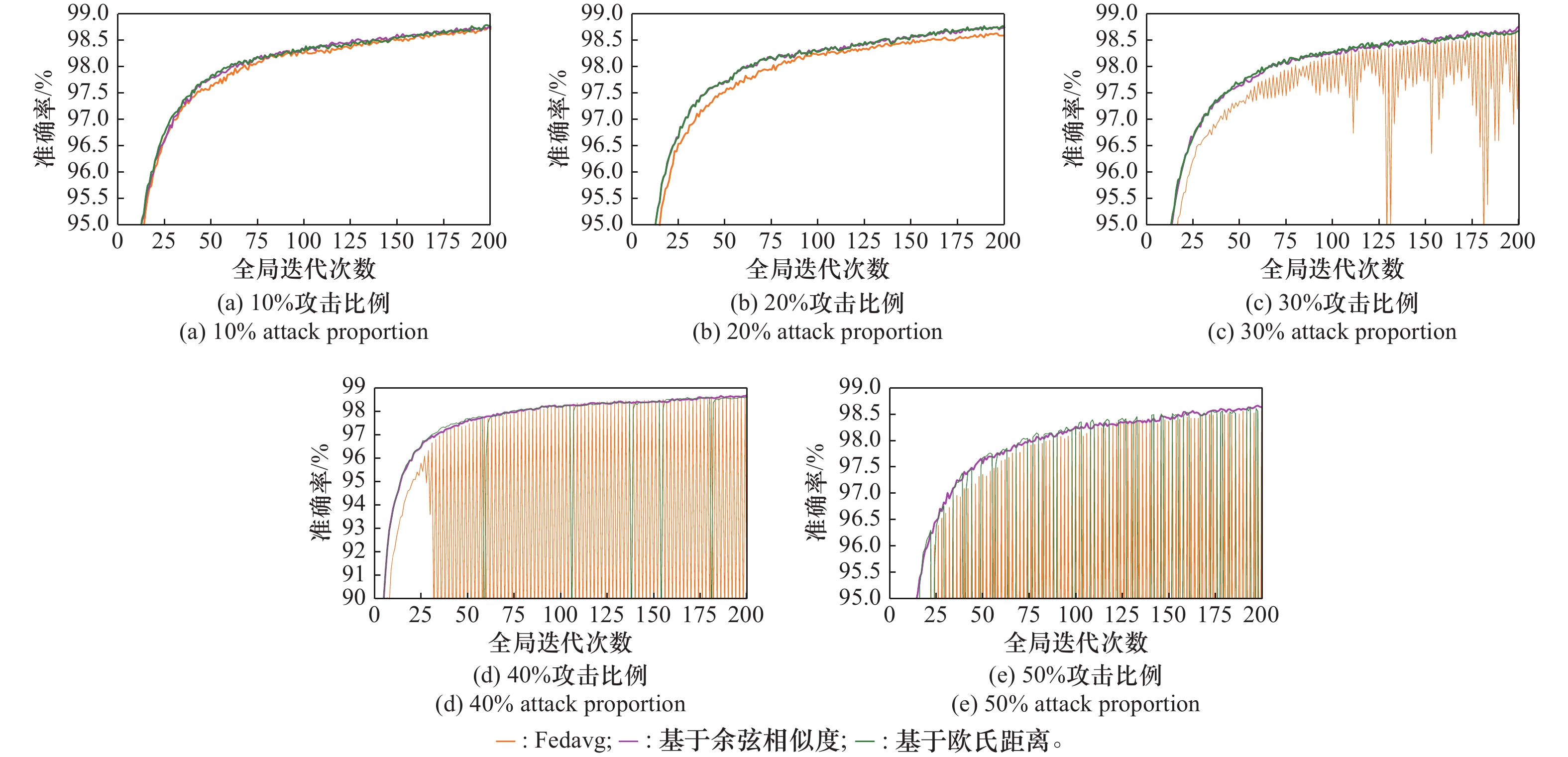
Comparison of different algorithm’s accuracy under different attack ratio on the MNIST dataset %"
| 算法 | 10%攻击比例 | 20%攻击比例 | 30%攻击比例 | 40%攻击比例 | 50%攻击比例 |
| FLDS-LFDPA | 98.72 | 98.69 | 98.75 | 98.56 | 98.59 |
| Fedavg | 98.68 | 98.60 | 97.92 | 93.64 | 93.94 |
| LFighter | 98.72 | 98.71 | 98.67 | 98.57 | 98.55 |
| Mkrum | 98.61 | 98.50 | 98.41 | 98.19 | 92.08 |
| FLAME | 98.33 | 98.36 | 98.16 | 97.57 | 95.87 |
| FoolsGold | 98.62 | 98.62 | 98.58 | 98.49 | 98.21 |
| Median | 98.40 | 98.41 | 98.35 | 98.09 | 93.23 |
| Tolpegin | 98.68 | 98.65 | 98.60 | 98.54 | 88.64 |
Table 2
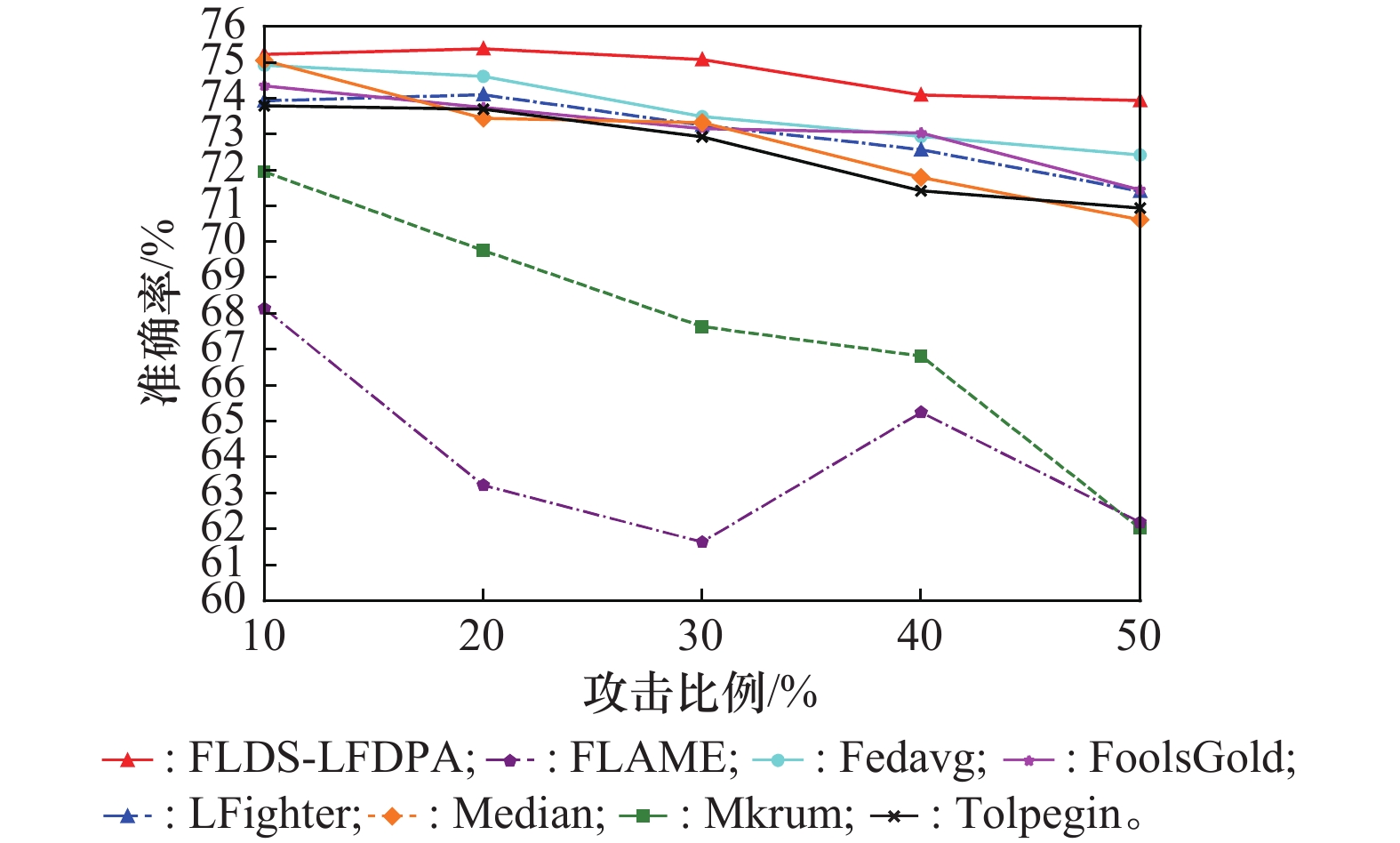
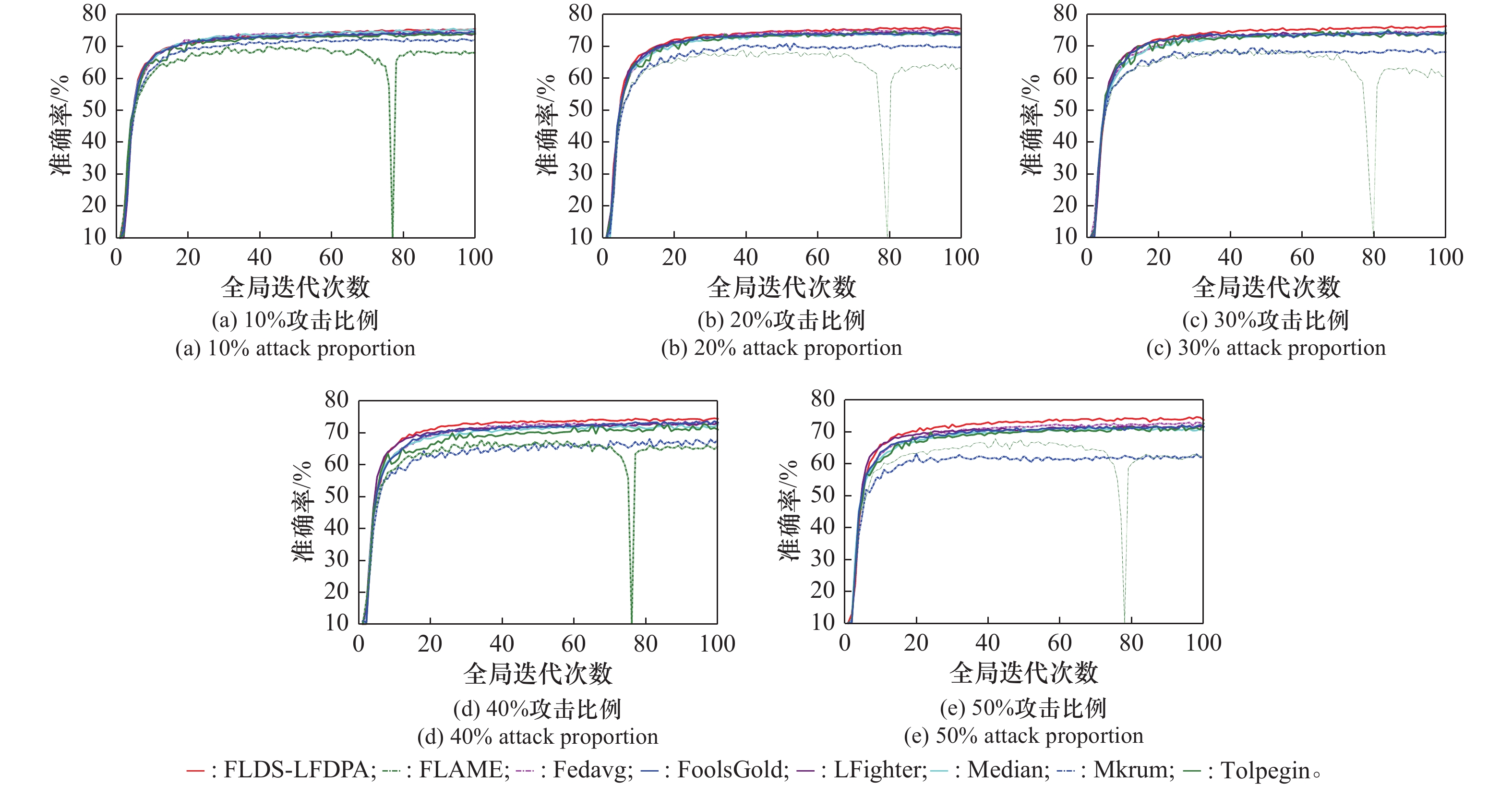
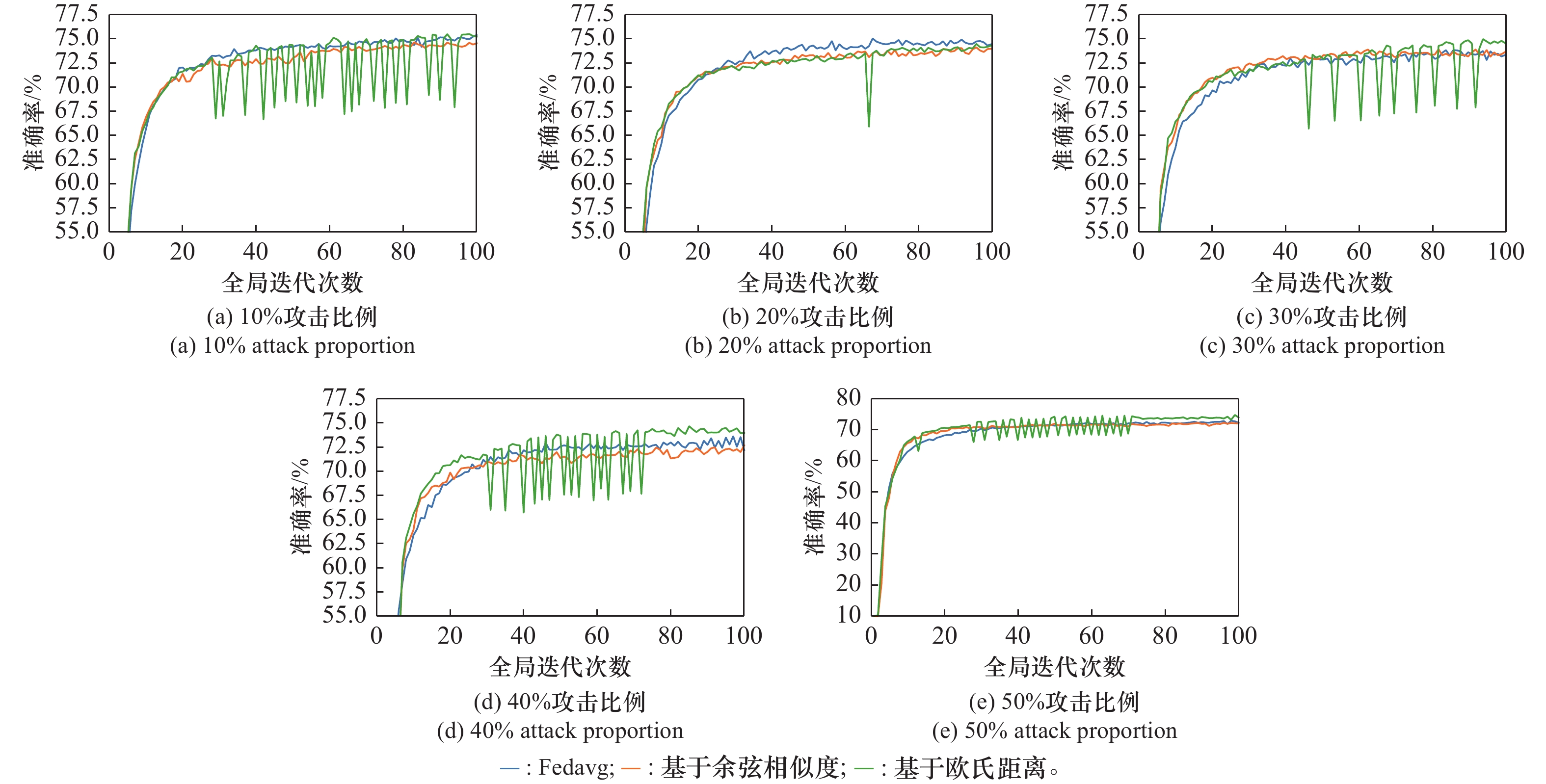
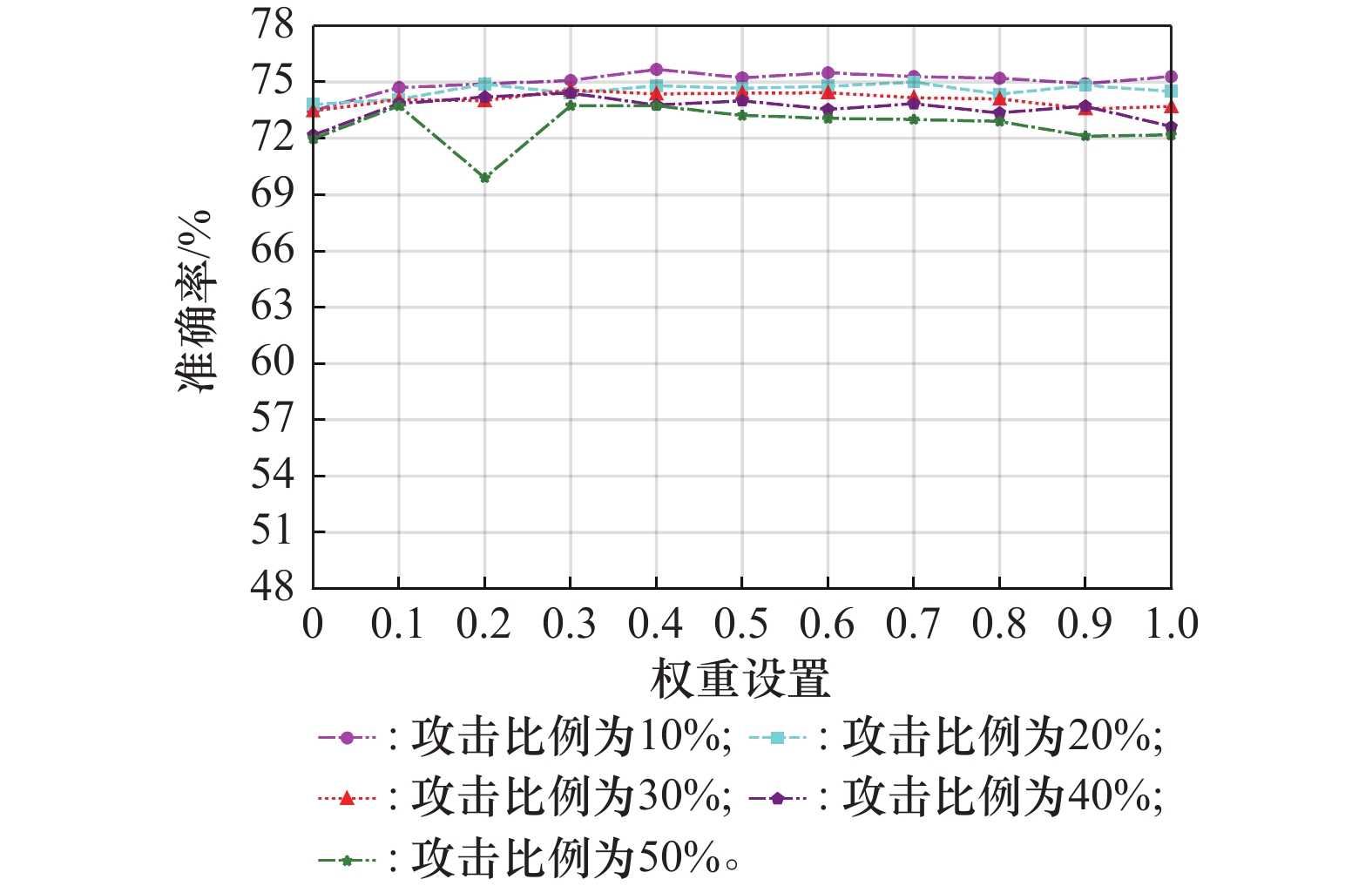
Comparison of different algorithm’s accuracy under different attack ratio on the CIFAR10 dataset %"
| 算法 | 10%攻击比例 | 20%攻击比例 | 30%攻击比例 | 40%攻击比例 | 50%攻击比例 |
| FLDS-LFDPA | 75.22 | 75.38 | 75.08 | 74.09 | 73.94 |
| Fedavg | 74.92 | 74.61 | 73.49 | 72.94 | 72.42 |
| LFighter | 73.93 | 74.10 | 73.25 | 72.57 | 71.41 |
| Mkrum | 71.95 | 69.76 | 67.64 | 66.82 | 62.02 |
| FLAME | 68.14 | 63.22 | 61.64 | 65.25 | 62.19 |
| FoolsGold | 74.35 | 73.74 | 73.16 | 73.03 | 71.45 |
| Median | 75.05 | 73.44 | 73.32 | 71.79 | 70.62 |
| Tolpegin | 73.79 | 73.70 | 72.92 | 71.42 | 70.94 |
| 1 | STRIPELIS D, AMBITE J L. Federated learning over harmonized data silos[C]// Proc. of the International Workshop on Health Intelligence, 2023: 27−41. |
| 2 |
WEN J, ZHANG Z X, LAN Y, et al. A survey on federated learning: challenges and applications[J]. International Journal of Machine Learning and Cybernetics, 2023, 14 (2): 513- 535.
doi: 10.1007/s13042-022-01647-y |
| 3 | MCMAHAN B, MOORE E, RAMAGE D, et al. Communication-efficient learning of deep networks from decentralized data[C]//Proc. of the Artificial Intelligence and Statistics, 2017: 1273−1282. |
| 4 |
SIKANDAR H S, WAHEED H, TAHIR S, et al. A detailed survey on federated learning attacks and defenses[J]. Electronics, 2023, 12 (2): 260.
doi: 10.3390/electronics12020260 |
| 5 | SHEJWALKAR V, HOUMANSADR A, KAIROUZ P, et al. Back to the drawing board: a critical evaluation of poisoning attacks on production federated learning [C]// Proc. of the IEEE Symposium on Security and Privacy , 2022: 1354−1371. |
| 6 | YANG Q. AI and data privacy protection: the way to federated learning[J]. Journal of Information Security Research, 2019, 5 (11): 961965. |
| 7 | WANG K Q, LIU J, LI C, et al. A survey on threats to federated learning[J]. Journal of Information Security Research, 2022, 8 (3): 223234. |
| 8 | BIGGIO B, NELSON B, LASKOV P. Poisoning attacks against support vector machines [C]//Proc. of the International Conference on Machine Learning, 2012: 1467−1474. |
| 9 | YANG Q, LIU Y, CHEN T J, et al. Federated machine learning: concept and applications[J]. ACM Transactions on Intelligent Systems and Technology, 2019, 10 (2): 1- 19. |
| 10 | NGUYEN D C, DING M, PATHIRANA P N, et al. Federated learning for internet of things: a comprehensive survey[J]. IEEE Communications Surveys & Tutorials, 2021, 23 (3): 1622- 1658. |
| 11 | ELBIR A M, SONER B, ÇOLERI S, et al. Federated learning in vehicular networks[C]// Proc. of the IEEE International Mediterranean Conference on Communications and Networking, 2022: 72−77. |
| 12 | SAYLAM B, INCE O D. Federated learning on edge sensing devices: a review[EB/OL].[2024-10-20]. https://arxiv.org/abs/2311.01201. |
| 13 | 肖雄, 唐卓, 肖斌, 等. 联邦学习的隐私保护与安全防御研究综述 [J]. 计算机学报, 2023, 46 (5): 1019−1044. |
| XIAO X, TANG Z, XIAO B, et al. Review of research on privacy rotection and security defense of federated learning[J]. Journal of Computer Science, 2023, 46 (5): 1019−1 044. | |
| 14 | MAMMEN P M. Federated learning: opportunities and challenges[EB/OL].[2024-10-20]. https://arxiv. org/abs/2101.05428. |
| 15 |
RODRIGUEZ-BARROSO N, JIMENEZ-LOPEZ D, LUZON M V, et al. Survey on federated learning threats: concepts, taxonomy on attacks and defences, experimental study and challenges[J]. Information Fusion, 2023, 90, 148- 173.
doi: 10.1016/j.inffus.2022.09.011 |
| 16 | CHEN H M, WANG H D, LONG Q Y, et al. Advancements in federated learning: models, methods, and privacy[J]. ACM Computing Surveys, 2024, 57 (2): 1- 39. |
| 17 |
HU K, GONG S, ZHANG Q, et al. An overview of implementing security and privacy in federated learning[J]. Artificial Intelligence Review, 2024, 57 (8): 204.
doi: 10.1007/s10462-024-10846-8 |
| 18 |
XIA G, CHEN J, YU C D, et al. Poisoning attacks in federated learning: a survey[J]. IEEE Access, 2023, 11, 10708- 10722.
doi: 10.1109/ACCESS.2023.3238823 |
| 19 | SUN G, CONG Y, DONG J H, et al. Data poisoning attacks on federated machine learning[J]. IEEE Internet of Things Journal, 2021, 9 (13): 11365- 11375. |
| 20 | ZHANG K Y, TAO G H, XU Q L, et al. FLIP: a provable defense framework for backdoor mitigation in federated learning[C]// Proc. of the International Conference on Learning Representations, 2022. |
| 21 | CAO D, CHANG S, LIN Z J, et al. Understanding distributed poisoning attack in federated learning [C]// Proc. of the IEEE 25th International Conference on Parallel and Distributed Systems, 2019: 233−239. |
| 22 | 田宇琛. 联邦学习环境下投毒攻击的防御方法研究[D]. 哈尔滨: 哈尔滨工业大学, 2021. |
| TIAN Y C. Research on defense methods against poisoning attacks in federated learning environment [D]. Harbin: Harbin Institute of Technology, 2021. | |
| 23 | TOLPEGIN V, TRUEX S, GURSOY M E, et al. Data poisoning attacks against federated learning systems[C]// Proc. of the European Symposium on Research in Computer Security, 2020: 480−501. |
| 24 | LI Z, WU X K, JIANG C J. Efficient poisoning attacks and defenses for unlabeled data in DDoS prediction of intelligent transportation systems[J]. Security and Safety, 2022, 1, 145- 165. |
| 25 | BLANCHARD P, MHAMDI E M E, GUERRAOUI R, et al. Machine learning with adversaries: byzantine tolerant gradient descent[C]// Proc. of the Advances in Neural Information Processing Systems, 2017: 119−129. |
| 26 | YIN D, CHEN Y D, KANNAN R, et al. Byzantine-robust distributed learning: towards optimal statistical rates[C]// Proc. of the International Conference on Machine Learning, 2018: 5650−5659. |
| 27 | 亢飞, 李建彬. 基于数据复杂度的投毒数据检测方法[J]. 计算机应用研究, 2020, 37 (7): 2140- 2143. |
| KANG F, LI J B. Method for detecting poisoning data based on data complexity[J]. Application Research of Computers, 2020, 37 (7): 2140- 2143. | |
| 28 | FUNG C, YOON C J M, BESCHASTNIKH I. The limitations of federated learning in sybil settings[C]// Proc. of the 23rd International Symposium on Research in Attacks, Intrusions and Defenses , 2020: 301−316. |
| 29 |
JEBREEL N M, DOMINGO-FERRER J, SANCHEZ D, et al. LFighter: defending against the label-flipping attack in federated learning[J]. Neural Networks, 2024, 170, 111- 126.
doi: 10.1016/j.neunet.2023.11.019 |
| 30 | 刘金全, 张铮, 陈自东, 等. 一种基于联邦学习参与方的投毒攻击防御方法[J]. 计算机应用研究, 2024, 41 (4): 1171- 1176. |
| LIU J Q, ZHANG Z, CHEN Z D, et al. Defense method on poisoning attack based on clients in federated learning[J]. Application Research of Computers, 2024, 41 (4): 1171- 1176. | |
| 31 | MACQUEEN J. Some methods for classification and analysis of multivariate observations[C]//Proc. of the 5th Berkeley Symposium on Mathematical Statistics and Probability, 1967. |
| 32 | 孔翎超, 刘国柱. 离群点检测算法综述[J]. 计算机科学, 2024, 51 (8): 20- 33. |
| KONG L C, LIU G Z. Review of outlier detection algorithms[J]. Computer Science, 2024, 51 (8): 20- 33. |
| [1] | Wenjie CHEN, Pu ZHANG, Gaoxiang SHI, Lin LIU, Xuan LIU. Blind recognition of LDPC codes based on the convolutional neural network with cosine check relationship [J]. Systems Engineering and Electronics, 2025, 47(9): 3117-3125. |
| [2] | Mingyu JIANG, Shunsheng ZHANG, Siyao XIAO. SAR target recognition based on lightweight cross-attention convolutional neural network [J]. Systems Engineering and Electronics, 2025, 47(9): 2853-2861. |
| [3] | Guoqing ZHANG, Yihui XU, Jiqiang LI, Xianku ZHANG, Bin QIU. Event-triggered control for USV-UAV based on asynchronous search guidance [J]. Systems Engineering and Electronics, 2025, 47(9): 3058-3065. |
| [4] | Geng HUANG, Dan LI, Jianqiu ZHANG. Robust zeroing neural network solution model for time-varying quadratic programming [J]. Systems Engineering and Electronics, 2025, 47(9): 2775-2784. |
| [5] | Wenqiang SHI, Yingke LEI, Hu JIN, Fei TENG. Algorithm for specific emitter identification based on adaptive wavelet decomposition and lightweight network architecture [J]. Systems Engineering and Electronics, 2025, 47(9): 2785-2796. |
| [6] | Qi WANG, Yuning PAN, Junfeng ZHENG, Li WANG. Implementation strategy of phased array beam control considering mechanical deformation [J]. Systems Engineering and Electronics, 2025, 47(8): 2421-2428. |
| [7] | Mengze ZHANG, Liyu TIAN. Radar target classification method based on high resolution spectral estimation [J]. Systems Engineering and Electronics, 2025, 47(7): 2146-2153. |
| [8] | Bo WEI, Caifu HU, Ruibin REN. Two-stage novel method for imbalanced data distribution in network intrusion detection [J]. Systems Engineering and Electronics, 2025, 47(6): 2065-2075. |
| [9] | Amin DUAN, Zhaohui ZHANG. Quadratic decomposition-based cellular traffic prediction with hybrid neural network [J]. Systems Engineering and Electronics, 2025, 47(5): 1687-1697. |
| [10] | Shujia PAN, Siguang CHEN. Communication-efficient decentralized federated learning with resource heterogeneity [J]. Systems Engineering and Electronics, 2025, 47(4): 1374-1383. |
| [11] | Kai CHEN, Deping ZHANG. Missile temporal planning method based on graph neural network [J]. Systems Engineering and Electronics, 2025, 47(3): 862-870. |
| [12] | Weihong FU, Xinyu ZHANG, Naian LIU. Single-channel blind source separation algorithm for co-frequency and co-modulation based on multi-scale fusion neural network [J]. Systems Engineering and Electronics, 2025, 47(2): 641-649. |
| [13] | Fang WU, Qingwei GAO, Ming WU, Shu AN. Deployment planning buoy polyline interception array based on GA-BP [J]. Systems Engineering and Electronics, 2025, 47(12): 4034-4039. |
| [14] | Jin TANG, Yishu WANG, Yangang LIANG, Haojian LI, Kebo LI. Research review of intelligent homing guidance law [J]. Systems Engineering and Electronics, 2025, 47(12): 4117-4129. |
| [15] | Lingchen KONG, Tongxin LIU, Chen ZHOU, Zhengyu ZHAO. Time-difference-of-arrival localization analysis based on regional ionospheric high resolution reconstruction [J]. Systems Engineering and Electronics, 2025, 47(11): 3521-3530. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||