Systems Engineering and Electronics ›› 2022, Vol. 44 ›› Issue (12): 3850-3862.doi: 10.12305/j.issn.1001-506X.2022.12.31
• Communications and Networks • Previous Articles Next Articles
Intrusion traffic detection and identification based on ADASYN and improved residual network
Xibo TANG1, Limin ZHANG1, Zhaogen ZHONG2,*
- 1. Department of Information Fusion, Naval Aviation University, Yantai 264001, China
2. School of Aviation Basis, Naval Aviation University, Yantai 264001, China
-
Received:2021-08-30Online:2022-11-14Published:2022-11-24 -
Contact:Zhaogen ZHONG
CLC Number:
Cite this article
Xibo TANG, Limin ZHANG, Zhaogen ZHONG. Intrusion traffic detection and identification based on ADASYN and improved residual network[J]. Systems Engineering and Electronics, 2022, 44(12): 3850-3862.
share this article
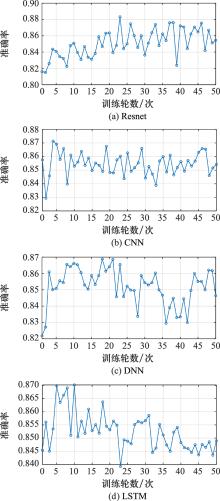
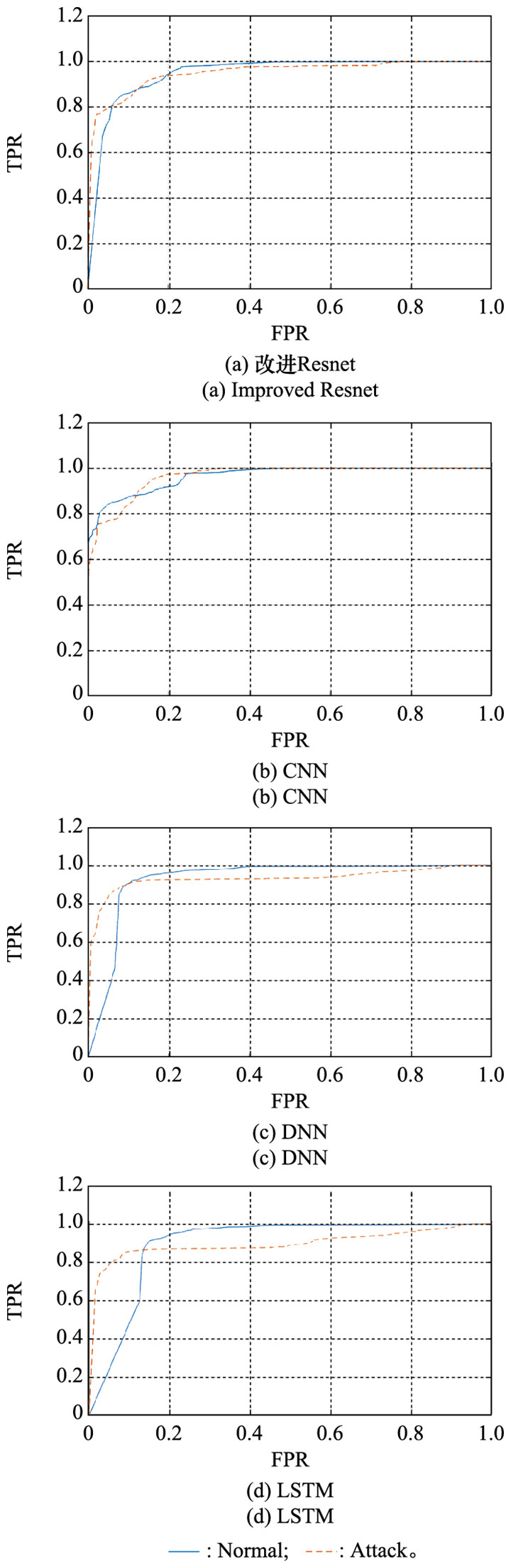
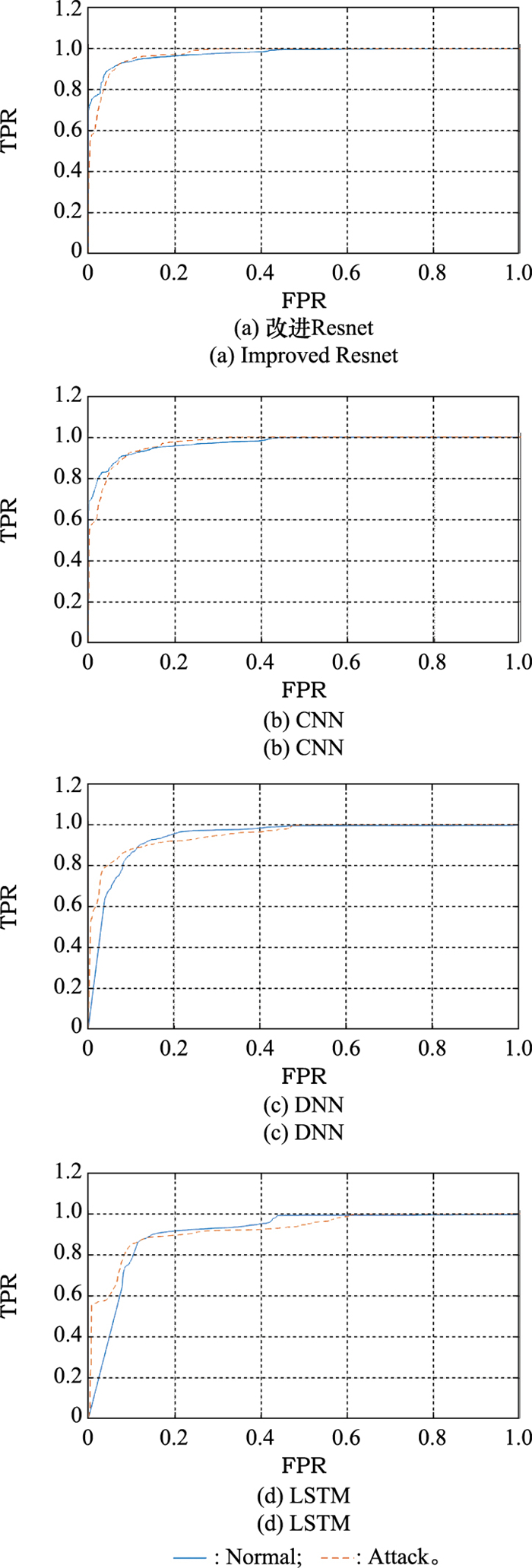
Table 3
Classical deep learning algorithm structure"
| 模型 | 结构 |
| CNN | Conv(32, 3, 3, 1, V)-RELU-Conv(64, 5, 5, 1, V)-RELU-MaxPool(2, 2, 1, V)-Conv(64, 4, 4, 1, V)-RELU-FC(256)-DR(0.5)-FC(m)-Softmax |
| LSTM | LSTM(128)-LSTM(128)-FC(256)-RELU-FC(m)-Softmax |
| DNN | FC(64)-RELU-FC(256)-RELU-FC(256)-RELU-FC(256)-RELU-DR(0.5)-FC(m)-Softmax |
Table 4
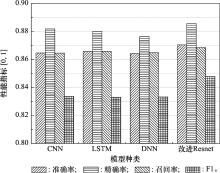
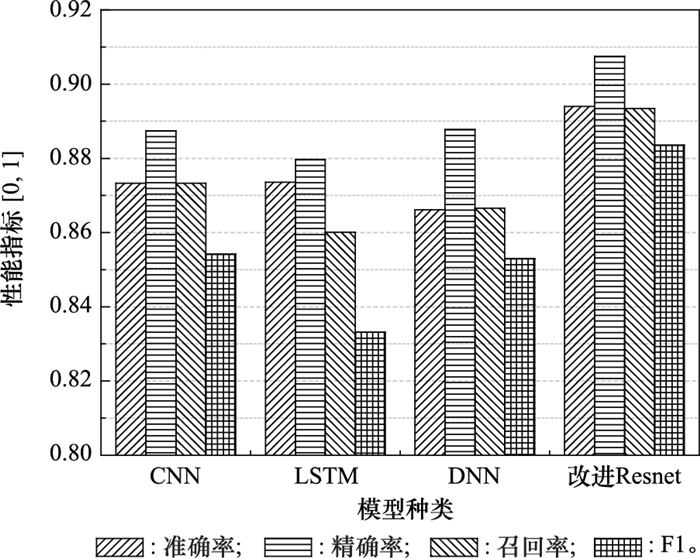
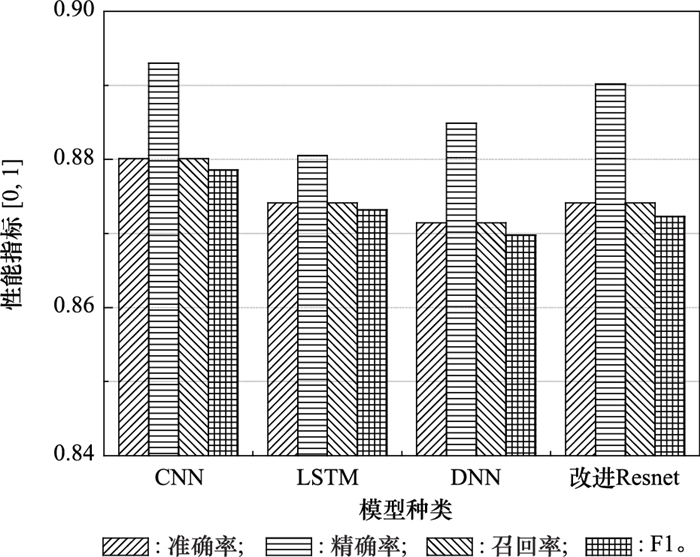
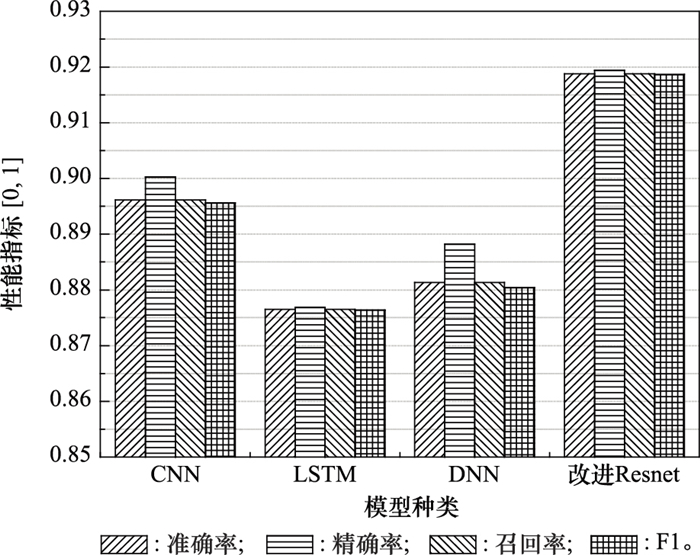
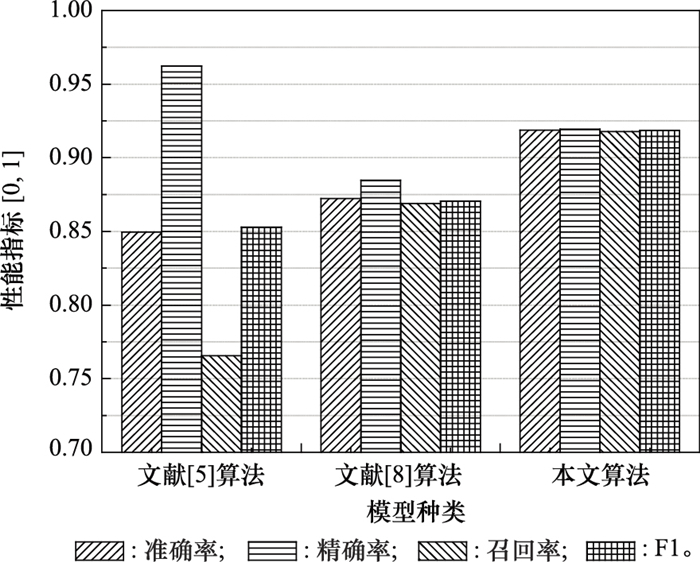
Comparison of performance indexes of each model %"
| 模型 | 原训练集 | 新训练集 | |||||||
| 准确率 | 精确率 | 召回率 | F1 | 准确率 | 精确率 | 召回率 | F1 | ||
| CNN | 86.47 | 88.19 | 86.46 | 83.36 | 87.33 | 88.75 | 87.33 | 85.42 | |
| LSTM | 86.58 | 88.01 | 86.58 | 83.30 | 87.36 | 87.97 | 86.01 | 83.32 | |
| DNN | 86.44 | 87.64 | 86.50 | 83.32 | 86.62 | 88.78 | 86.66 | 85.30 | |
| 改进Resnet | 87.05 | 88.56 | 86.85 | 84.78 | 89.40 | 90.75 | 89.35 | 88.36 | |
Table 5
Improved Resnet confusion matrix without oversampling (multi-classification)"
| 流量 | 流量 | ||||
| Normal | DoS | Probing | R2L | U2R | |
| Normal | 9 304 | 71 | 331 | 5 | 0 |
| DoS | 68 | 5 496 | 177 | 0 | 0 |
| Probing | 125 | 0 | 981 | 0 | 0 |
| R2L | 1 478 | 84 | 96 | 541 | 0 |
| U2R | 30 | 0 | 4 | 3 | 0 |
| 精确率 | 0.845 4 | 0.972 6 | 0.617 4 | 0.985 4 | 0.000 0 |
| 召回率 | 0.958 1 | 0.957 3 | 0.887 0 | 0.246 0 | 0.000 0 |
Table 6
Improved Resnet confusion matrix with oversampling (multi-classification)"
| 流量 | 流量 | ||||
| Normal | DoS | Probing | R2L | U2R | |
| Normal | 9 296 | 83 | 292 | 22 | 18 |
| DoS | 75 | 5 590 | 76 | 0 | 0 |
| Probing | 67 | 1 | 1 038 | 0 | 0 |
| R2L | 1 164 | 0 | 111 | 850 | 74 |
| U2R | 12 | 0 | 1 | 5 | 19 |
| 精确率 | 0.875 8 | 0.985 2 | 0.683 8 | 0.969 2 | 0.171 2 |
| 召回率 | 0.957 3 | 0.973 7 | 0.938 5 | 0.386 5 | 0.513 5 |
| 1 |
MUKHERJEE B , HEBERLEIN L T , LEVITT K N . Network intrusion detection[J]. IEEE Network, 1994, 8 (3): 26- 41.
doi: 10.1109/65.283931 |
| 2 | AHMAD Z , KHAN A S , SHIANG C W , et al. Network intrusion detection system: a systematic study of machine learning and deep learning approaches[J]. Transactions on Emerging Telecommunications Technologies, 2021, 32 (1): e4150. |
| 3 | DAINOTTI A, GARGIULO F, KUNCHEVA L I, et al. Identification of traffic flows hiding behind TCP port 80[C]//Proc. of the IEEE International Conference on Communication, 2010. |
| 4 | MEHMOOD T, RAIS H B M. SVM for network anomaly detection using ACO feature subset[C]//Proc. of the IEEE International Symposium on Mathematical Sciences and Computing Research, 2015: 121-126. |
| 5 |
AL-QATF M , YU L S , AL-HABIB M , et al. Deep learning approach combining sparse autoencoder with SVM for network intrusion detection[J]. IEEE Access, 2018, 6, 52843- 52856.
doi: 10.1109/ACCESS.2018.2869577 |
| 6 |
GAO X W , SHAN C Z , HU C , et al. An adaptive ensemble machine learning model for intrusion detection[J]. IEEE Access, 2019, 7, 82512- 82521.
doi: 10.1109/ACCESS.2019.2923640 |
| 7 |
LECUNY , BENGIO Y , HINTON G . Deep learning[J]. Nature, 2015, 521, 436.
doi: 10.1038/nature14539 |
| 8 |
SU T T , SUN H Z , ZHU J Q , et al. BAT: deep learning methods on network intrusion detection using NSL-KDD dataset[J]. IEEE Access, 2020, 8, 29575- 29585.
doi: 10.1109/ACCESS.2020.2972627 |
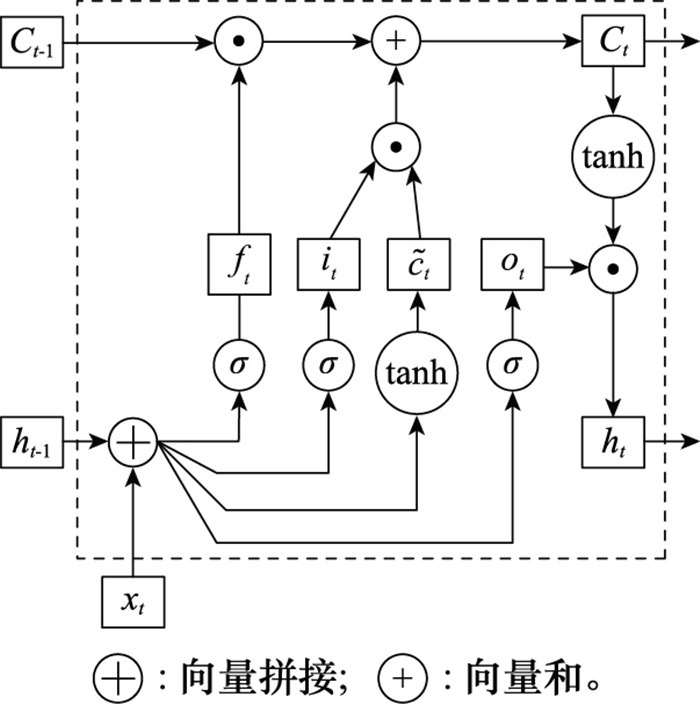
| 9 | 麻文刚, 张亚东, 郭进. 基于LSTM与改进残差网络优化的异常流量检测方法[J]. 通信学报, 2021, 42 (5): 23- 40. |
| MA W G , ZHANG Y D , GUO J . Abnormal traffic detection method based on LSTM and improved residual neural network optimization[J]. Journal of Communications, 2021, 42 (5): 23- 40. | |
| 10 |
GURUNG S , GHOSE M K , SUBEDI A . Deep learning approach on network intrusion detection system using NSL-KDD dataset[J]. International Journal of Computer Network and Information Security, 2019, 11 (3): 8- 14.
doi: 10.5815/ijcnis.2019.03.02 |
| 11 |
ZAVRAK S , ISKEFIYELI M . Anomaly-based intrusion detection from network flow features using variational autoencoder[J]. IEEE Access, 2020, 8, 108346- 108358.
doi: 10.1109/ACCESS.2020.3001350 |
| 12 | AUREÉLIEN G . Neural networks and deep learning[M]. Cham: Springer, 2018: 79- 81. |
| 13 | LE T, KIM J, KIM H. An effective intrusion detection classifier using long short-term memory with gradient descent optimization[C]//Proc. of the IEEE International Conference on Platform Technology and Service, 2017. |
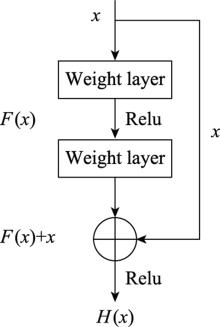
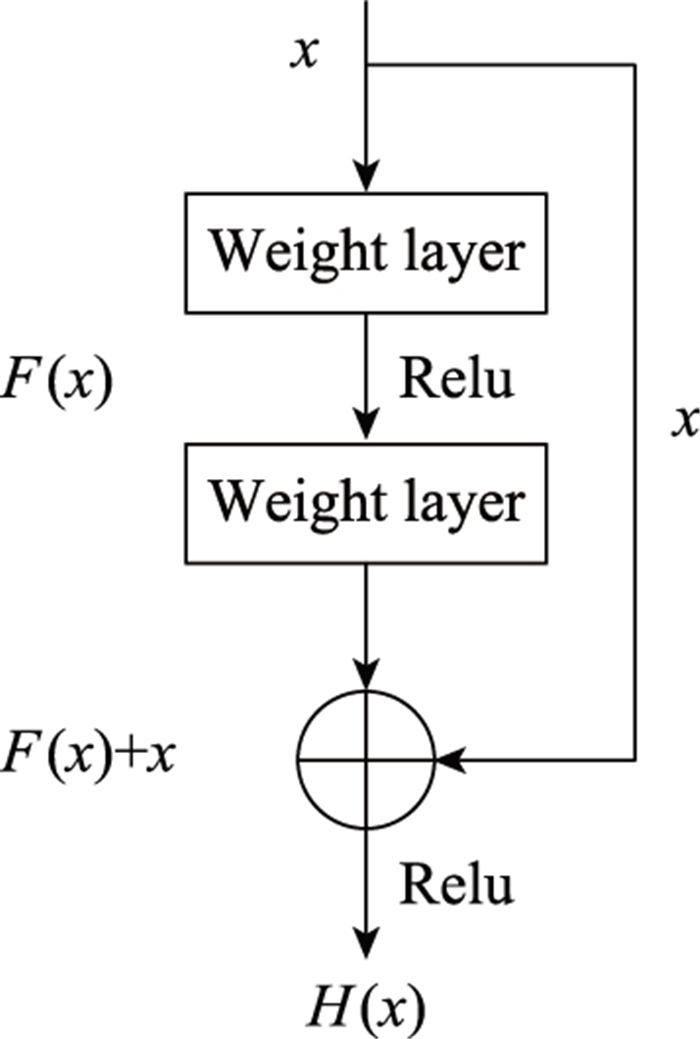
| 14 | HE K M, ZHANG X Y, REN S Q, et al. Identity mappings in deep residual networks[C]//Proc. of the European Conference on Computer Vision, 2016: 630-645. |
| 15 | HE K M, ZHANG X Y, REN S Q, et al. Deep residual learning for image recognition[C]//Proc. of the IEEE Conference on Computer Vision And Pattern Recognition, 2016: 770-778. |
| 16 |
XIAO Y L , XIAO X . An intrusion detection system based on a simplified residual network[J]. Information, 2019, 10 (11): 356.
doi: 10.3390/info10110356 |
| 17 | 时东阁. 基于深度学习的入侵检测方法研究[D]. 郑州: 郑州大学, 2019. |
| SHI D G. Research on intrusion detection method based on deep learning[D]. Zhengzhou: Zhengzhou University, 2019. | |
| 18 |
AL-DAWERI M S , ZAINOLARIFFIN K A , ABDULLAH S . An analysis of the KDD99 and UNSW-NB15 datasets for the intrusion detection system[J]. Symmetry, 2020, 12 (10): 1666.
doi: 10.3390/sym12101666 |
| 19 | FARHAT S, ABDELKADER M, MEDDEB-MAKHLOUF A, et al. Comparative study of classification algorithms for cloud IDS using NSL-KDD dataset in WEKA[C]//Proc. of the IEEE International Wireless Communications and Mobile Computing, 2020: 445-450. |
| 20 | RING M , WUNDERLICH S , SCHEURING D , et al. A survey of network-based intrusion detection data sets[J]. Computers & Security, 2019, 86, 147- 167. |
| 21 | ABRAR I, AYUB Z, MASOODI F, et al. A machine learning approach for intrusion detection system on NSL-KDD dataset[C]//Proc. of the IEEE International Conference on Smart Electronics and Communication, 2020: 919-924. |
| 22 |
HU Z Q , WANG L J , QI L , et al. A novel wireless network intrusion detection method based on adaptive synthetic sampling and an improved convolutional neural network[J]. IEEE Access, 2020, 8, 195741- 195751.
doi: 10.1109/ACCESS.2020.3034015 |
| 23 | 王健. 网络异常检测的关键技术研究[D]. 南京: 南京邮电大学, 2020. |
| WANG J. Research on key technologies of network anomaly detection[D]. Nanjing: Nanjing University of Posts and Telecommunications, 2020. | |
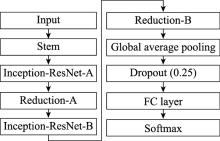
| 24 | SZEGEDY C, IOFFE S, VANHOUCKE V, et al. Inception-v4, inception-resnet and the impact of residual connections on learning[C]//Proc. of the 31st AAAI Conference on Artificial Intelligence, 2017: 4278-4284. |
| 25 |
JIANG K Y , WANG W Y , WANG A L , et al. Network intrusion detection combined hybrid sampling with deep hierarchical network[J]. IEEE Access, 2020, 8, 32464- 32476.
doi: 10.1109/ACCESS.2020.2973730 |
| 26 |
ZAVRAK S , ISKEFIYELI M . Anomaly-based intrusion detection from network flow features using variational autoencoder[J]. IEEE Access, 2020, 8, 108346- 108358.
doi: 10.1109/ACCESS.2020.3001350 |
| [1] | Cunxiang XIE, Limin ZHANG, Zhaogen ZHONG. Radar signal recognition based on time-frequency feature extraction and residual neural network [J]. Systems Engineering and Electronics, 2021, 43(4): 917-926. |
| [2] | Yicong SUN, Runlan TIAN, Huixu DONG, Liang SUN. Polyphase code signal recognition method based on SAMME+ResNet [J]. Systems Engineering and Electronics, 2020, 42(10): 2239-2245. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||